ZyXEL P-202H User Guide - Page 330
Table 122, Table 123, Table 121
 |
View all ZyXEL P-202H manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 330 highlights
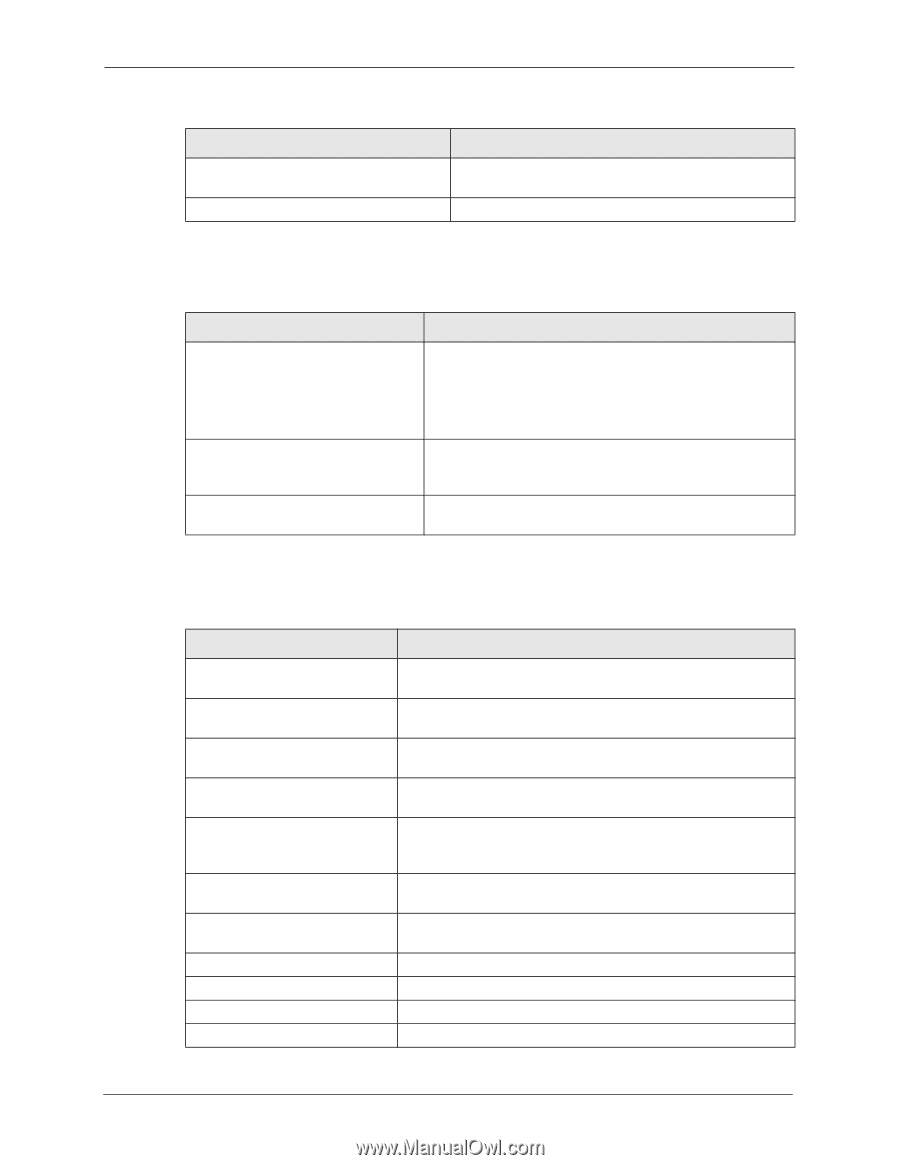
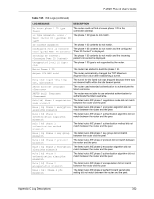
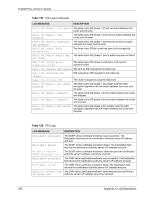
P-202H Plus v2 User's Guide Table 121 ICMP Logs (continued) LOG MESSAGE Unsupported/out-of-order ICMP: ICMP Router reply ICMP packet: ICMP DESCRIPTION The firewall does not support this kind of ICMP packets or the ICMP packets are out of order. The router sent an ICMP reply packet to the sender. Table 122 CDR Logs LOG MESSAGE DESCRIPTION board%d line%d channel%d, call%d,%s C01 Outgoing Call dev=%x ch=%x%s The router received the setup requirements for a call. "call" is the reference (count) number of the call. "dev" is the device type (3 is for dial-up, 6 is for PPPoE, 10 is for PPTP). "channel" or "ch" is the call channel ID.For example,"board 0 line 0 channel 0, call 3, C01 Outgoing Call dev=6 ch=0 "Means the router has dialed to the PPPoE server 3 times. board%d line%d channel%d, call%d,%s C02 OutCall Connected%d%s The PPPoE, PPTP or dial-up call is connected. board%d line%d channel%d, The PPPoE, PPTP or dial-up call was disconnected. call%d,%s C02 Call Terminated Table 123 Attack Logs LOG MESSAGE DESCRIPTION attack [TCP | UDP | IGMP | ESP | GRE | OSPF] attack ICMP (type:%d, code:%d) land [TCP | UDP | IGMP | ESP | GRE | OSPF] land ICMP (type:%d, code:%d) ip spoofing - WAN [TCP | UDP | IGMP | ESP | GRE | OSPF] ip spoofing - WAN ICMP (type:%d, code:%d) icmp echo: ICMP (type:%d, code:%d) syn flood TCP ports scan TCP teardrop TCP teardrop UDP The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF attack. The firewall detected an ICMP attack. For type and code details, see Table 129 on page 336. The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF land attack. The firewall detected an ICMP land attack. For type and code details, see Table 129 on page 336. The firewall detected an IP spoofing attack on the WAN port. The firewall detected an ICMP IP spoofing attack on the WAN port. For type and code details, see Table 129 on page 336. The firewall detected an ICMP echo attack. For type and code details, see Table 129 on page 336. The firewall detected a TCP syn flood attack. The firewall detected a TCP port scan attack. The firewall detected a TCP teardrop attack. The firewall detected an UDP teardrop attack. 329 Appendix C Log Descriptions