ZyXEL P-202H User Guide - Page 316
Table 106
 |
View all ZyXEL P-202H manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 316 highlights
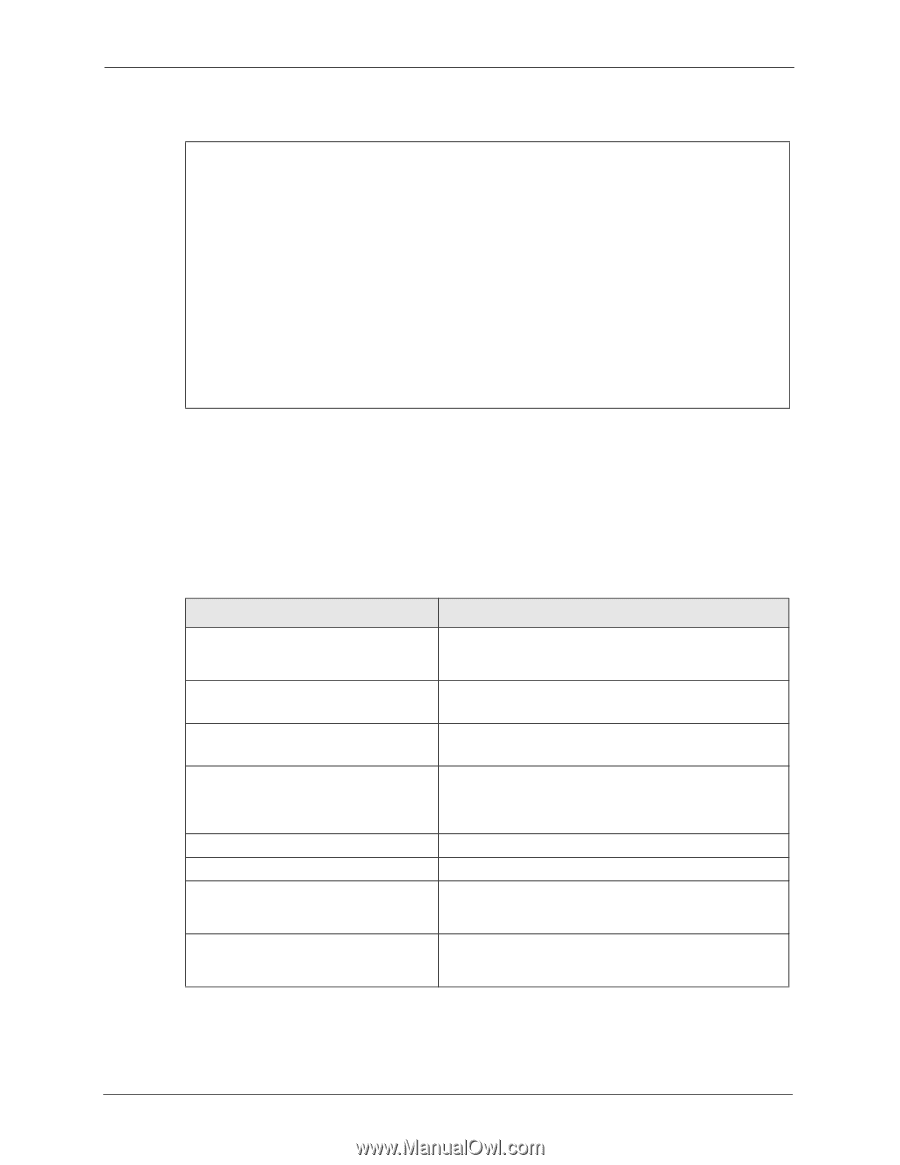
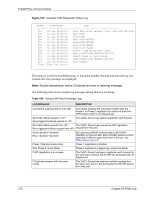
P-202H Plus v2 User's Guide Figure 210 Example VPN Responder IPSec Log Index: Date/Time: Log: 001 01 Jan 08:08:07 Recv Main Mode request from 002 01 Jan 08:08:07 Recv: 003 01 Jan 08:08:08 Send: 004 01 Jan 08:08:08 Recv: 005 01 Jan 08:08:10 Send: 006 01 Jan 08:08:10 Recv: 007 01 Jan 08:08:10 Send: 008 01 Jan 08:08:10 Phase 1 IKE SA process done 009 01 Jan 08:08:10 Recv: 010 01 Jan 08:08:10 Start Phase 2: Quick Mode 011 01 Jan 08:08:10 Send: 012 01 Jan 08:08:10 Recv: Clear IPSec Log (y/n): This menu is useful for troubleshooting. A log index number, the date and time the log was created and a log message are displayed. Note: Double exclamation marks (!!) denote an error or warning message. The following table shows sample log messages during IKE key exchange. Table 106 Sample IKE Key Exchange Logs LOG MESSAGE DESCRIPTION Cannot find outbound SA for rule Send Main Mode request to Send Aggressive Mode request to The packet matches the rule index number (#d), but Phase 1 or Phase 2 negotiation for outbound (from the VPN initiator) traffic is not finished yet. The ZyXEL Device has started negotiation with the peer. Recv Main Mode request from The ZyXEL Device has received an IKE negotiation Recv Aggressive Mode request from request from the peer. Send: Recv: IKE uses the ISAKMP protocol (refer to RFC2408 ISAKMP) to transmit data. Each ISAKMP packet contains payloads of different types that show in the log - see Table 108 on page 317. Phase 1 IKE SA process done Start Phase 2: Quick Mode Phase 1 negotiation is finished. Phase 2 negotiation is beginning using Quick Mode. !! IKE Negotiation is in process The ZyXEL Device has begun negotiation with the peer for the connection already, but the IKE key exchange has not finished yet. !! Duplicate requests with the same cookie The ZyXEL Device has received multiple requests from the same peer but it is still processing the first IKE packet from that peer. 315 Chapter 35 IPSec Log