ZyXEL UAG715 User Guide - Page 251
Table 97, Source, Destination, Schedule, Service, Action
 |
View all ZyXEL UAG715 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 251 highlights
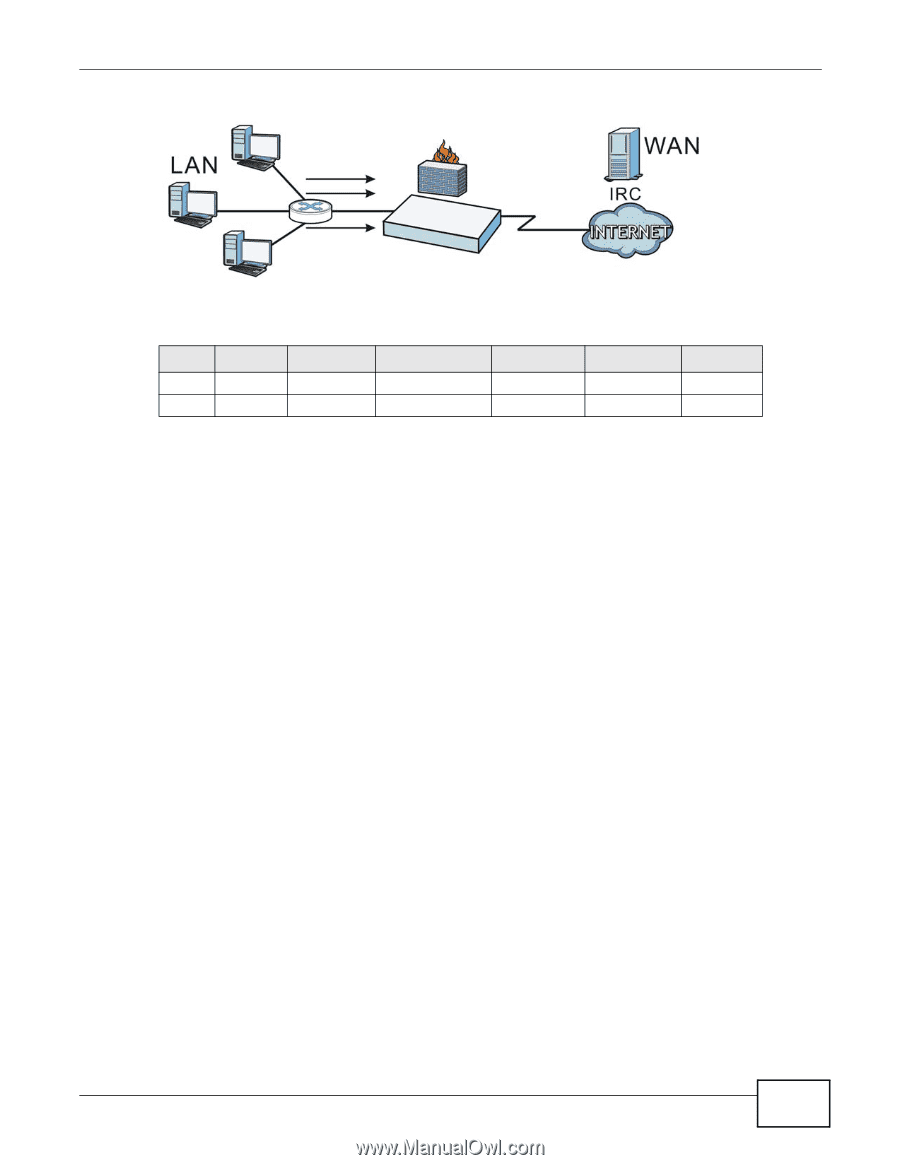
Figure 171 Blocking All LAN to WAN IRC Traffic Example Chapter 21 Firewall Your firewall would have the following rules. Table 97 Blocking All LAN to WAN IRC Traffic Example # USER SOURCE DESTINATION SCHEDULE 1 Any Any Any Any 2 Any Any Any Any SERVICE IRC Any ACTION Deny Allow • The first row blocks LAN access to the IRC service on the WAN. • The second row is the firewall's default policy that allows all LAN1 to WAN traffic. The UAG applies the firewall rules in order. So for this example, when the UAG receives traffic from the LAN, it checks it against the first rule. If the traffic matches (if it is IRC traffic) the firewall takes the action in the rule (drop) and stops checking the firewall rules. Any traffic that does not match the first firewall rule will match the second rule and the UAG forwards it. Now suppose you need to let the CEO use IRC. You configure a LAN1 to WAN firewall rule that allows IRC traffic from the IP address of the CEO's computer. You can also configure a LAN to WAN rule that allows IRC traffic from any computer through which the CEO logs into the UAG with his/her user name. In order to make sure that the CEO's computer always uses the same IP address, make sure it either: • Has a static IP address, or • You configure a static DHCP entry for it so the UAG always assigns it the same IP address (see DHCP Settings on page 139 for information on DHCP). Now you configure a LAN1 to WAN firewall rule that allows IRC traffic from the IP address of the CEO's computer (192.168.1.7 for example) to go to any destination address. You do not need to specify a schedule since you want the firewall rule to always be in effect. The following figure shows the results of your two custom rules. UAG715 User's Guide 251