ZyXEL UAG715 User Guide - Page 327
ADP Technical Reference
 |
View all ZyXEL UAG715 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 327 highlights
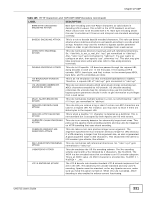
Chapter 27 ADP Table 124 Configuration > ADP > Profile > Protocol Anomaly (continued) LABEL DESCRIPTION Cancel Click Cancel to return to the profile summary page without saving any changes. Save Click Save to save the configuration to the UAG but remain in the same page. You may then go to the another profile screen (tab) in order to complete the profile. Click OK in the final profile screen to complete the profile. 27.4 ADP Technical Reference This section is divided into traffic anomaly background information and protocol anomaly background information. Traffic Anomaly Background Information The following sections may help you configure the traffic anomaly profile screen (Section 27.3.4 on page 321). Port Scanning An attacker scans device(s) to determine what types of network protocols or services a device supports. One of the most common port scanning tools in use today is Nmap. Many connection attempts to different ports (services) may indicate a port scan. These are some port scan types: • TCP Portscan • UDP Portscan • IP Portscan An IP port scan searches not only for TCP, UDP and ICMP protocols in use by the remote computer, but also additional IP protocols such as EGP (Exterior Gateway Protocol) or IGP (Interior Gateway Protocol). Determining these additional protocols can help reveal if the destination device is a workstation, a printer, or a router. Decoy Port Scans Decoy port scans are scans where the attacker has spoofed the source address. These are some decoy scan types: • TCP Decoy Portscan • UDP Decoy Portscan • IP Decoy Portscan Distributed Port Scans Distributed port scans are many-to-one port scans. Distributed port scans occur when multiple hosts query one host for open services. This may be used to evade intrusion detection. These are distributed port scan types: UAG715 User's Guide 327