ZyXEL UAG715 User Guide - Page 289
Table 110, Label, Description
 |
View all ZyXEL UAG715 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 289 highlights
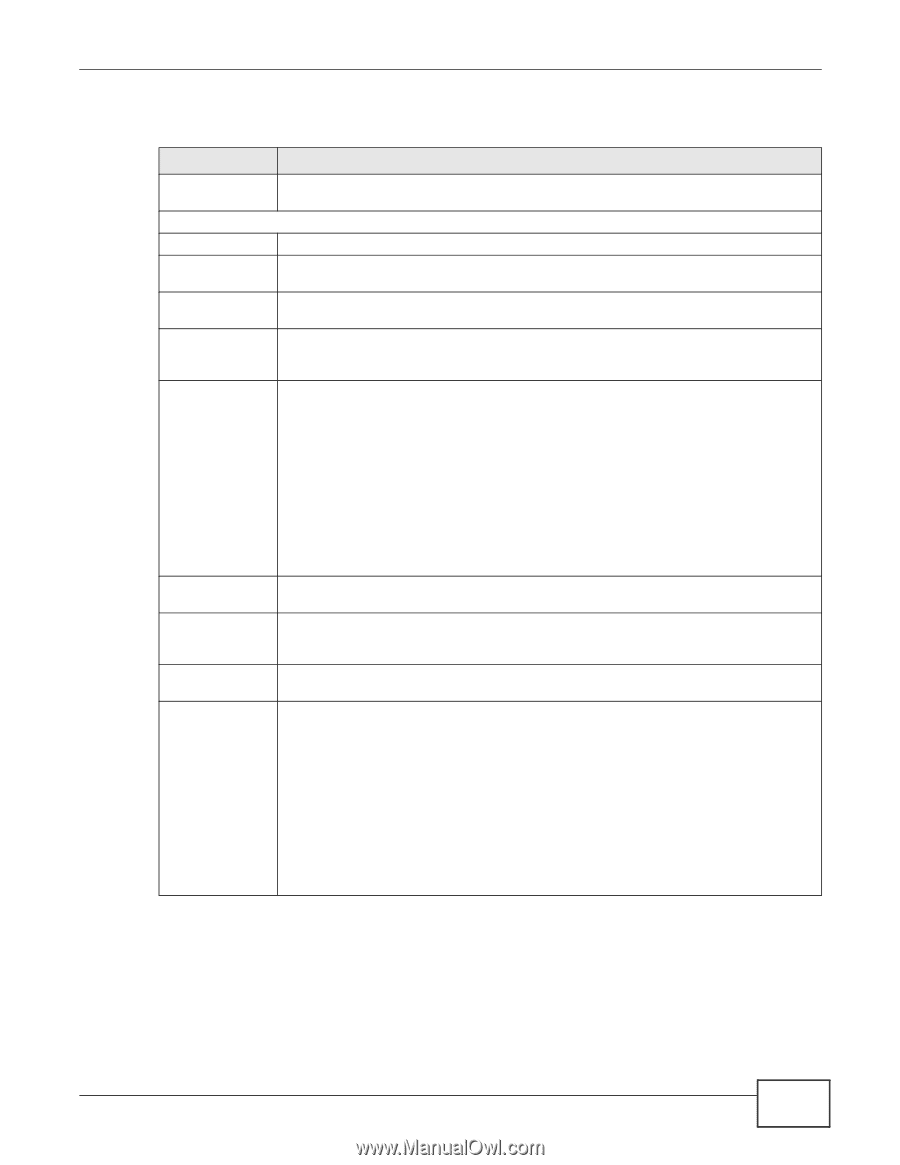
Chapter 23 SSL VPN The following table describes the labels in this screen. Table 110 VPN > SSL VPN > Access Privilege > Add/Edit LABEL Create new Object Configuration Enable Policy Name Description Clean browser cache when user logs out User/Group DESCRIPTION Use to configure any new settings objects that you need to use in this screen. Select this option to activate this SSL access policy. Enter a descriptive name to identify this policy. You can enter up to 31 characters ("a-z", A-Z", "0-9") with no spaces allowed. Enter additional information about this SSL access policy. You can enter up to 60 characters ("0-9", "a-z", "A-Z", "-" and "_"). Select this to clean the cookie, history, and temporary Internet files in the user's browser's cache when the user logs out. The UAG returns them to the values present before the user logged in. The Selectable User/Group Objects list displays the name(s) of the user account and/ or user group(s) to which you have not applied an SSL access policy yet. To associate a user or user group to this SSL access policy, select a user account or user group and click the right arrow button to add to the Selected User/Group Objects list. You can select more than one name. To remove a user or user group, select the name(s) in the Selected User/Group Objects list and click the left arrow button. Endpoint Security (EPS) Enable EPS Checking Periodical checking time Available EPS Objects / Selected EPS Objects Note: Although you can select admin and limited-admin accounts in this screen, they are reserved for device configuration only. You cannot use them to access the SSL VPN portal. Use these fields to make sure users' computers meet an endpoint security object's Operating System (OS) and security requirements before granting access. Select this to have the UAG check that users' computers meet the Operating System (OS) and security requirements of one of the SSL access policy's selected endpoint security objects before granting access. Select this and specify a number of minutes to have the UAG repeat the endpoint security check at a regular interval. Configured endpoint security objects appear on the left. Select the endpoint security objects to use for this SSL access policy and click the right arrow button to add them to the selected list on the right. Use the [Shift] and/or [Ctrl] key to select multiple objects. Select any endpoint security objects that you want to remove from the selected list and click the left arrow button to remove them. The UAG checks authenticated users' computers against the SSL access policy's selected endpoint security objects in the order you list them here. When a user's computer matches an endpoint security object the UAG grants access and stops checking. Select an endpoint security object and use the up and down arrows to change it's position in the list. To make the endpoint security check as efficient as possible, arrange the endpoint security objects in order with the one that the most users should match first and the one that the least users should match last. UAG715 User's Guide 289