ZyXEL UAG715 User Guide - Page 331
Table 125, Label, Description
 |
View all ZyXEL UAG715 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 331 highlights
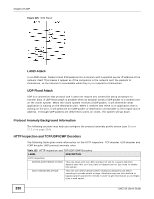
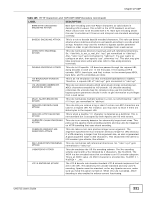
Chapter 27 ADP Table 125 HTTP Inspection and TCP/UDP/ICMP Decoders (continued) LABEL DESCRIPTION BARE-BYTE-UNICODINGENCODING ATTACK Bare byte encoding uses non-ASCII characters as valid values in decoding UTF-8 values. This is NOT in the HTTP standard, as all nonASCII values have to be encoded with a %. Bare byte encoding allows the user to emulate an IIS server and interpret non-standard encodings correctly. BASE36-ENCODING ATTACK This is a rule to decode base36-encoded characters. This rule can detect attacks where malicious attackers use base36-encoding to encode attack strings. Attackers may use this method to bypass system parameter checks in order to get information or privileges from a web server. DIRECTORY-TRAVERSAL ATTACK This rule normalizes directory traversals and self-referential directories. So, "/abc/this_is_not_a_real_dir/../xyz" get normalized to "/abc/xyz". Also, "/abc/./xyz" gets normalized to "/abc/xyz". If a user wants to configure an alert, then specify "yes", otherwise "no". This alert may give false positives since some web sites refer to files using directory traversals. DOUBLE-ENCODING ATTACK This rule is IIS specific. IIS does two passes through the request URI, doing decodes in each one. In the first pass, IIS encoding (UTF-8 unicode, ASCII, bare byte, and %u) is done. In the second pass ASCII, bare byte, and %u encodings are done. IIS-BACKSLASH-EVASION ATTACK This is an IIS emulation rule that normalizes backslashes to slashes. Therefore, a request-URI of "/abc\xyz" gets normalized to "/abc/xyz". IIS-UNICODE-CODEPOINTENCODING ATTACK This rule can detect attacks which send attack strings containing nonASCII characters encoded by IIS Unicode. IIS Unicode encoding references the unicode.map file. Attackers may use this method to bypass system parameter checks in order to get information or privileges from a web server. MULTI-SLASH-ENCODING ATTACK This rule normalizes multiple slashes in a row, so something like: "abc/// //////xyz" get normalized to "abc/xyz". NON-RFC-DEFINED-CHAR ATTACK This rule lets you receive a log or alert if certain non-RFC characters are used in a request URI. For instance, you may want to know if there are NULL bytes in the request-URI. NON-RFC-HTTP-DELIMITER ATTACK This is when a newline "\n" character is detected as a delimiter. This is non-standard but is accepted by both Apache and IIS web servers. OVERSIZE-CHUNK-ENCODING ATTACK This rule is an anomaly detector for abnormally large chunk sizes. This picks up the apache chunk encoding exploits and may also be triggered on HTTP tunneling that uses chunk encoding. OVERSIZE-REQUEST-URIDIRECTORY ATTACK This rule takes a non-zero positive integer as an argument. The argument specifies the max character directory length for URL directory. If a URL directory is larger than this argument size, an alert is generated. A good argument value is 300 characters. This should limit the alerts to IDS evasion type attacks, like whisker. SELF-DIRECTORY-TRAVERSAL This rule normalizes self-referential directories. So, "/abc/./xyz" gets ATTACK normalized to "/abc/xyz". U-ENCODING ATTACK This rule emulates the IIS %u encoding scheme. The %u encoding scheme starts with a %u followed by 4 characters, like %uXXXX. The XXXX is a hex encoded value that correlates to an IIS unicode codepoint. This is an ASCII value. An ASCII character is encoded like, %u002f = /, %u002e = ., etc. UTF-8-ENCODING ATTACK The UTF-8 decode rule decodes standard UTF-8 unicode sequences that are in the URI. This abides by the unicode standard and only uses % encoding. Apache uses this standard, so for any Apache servers, make sure you have this option turned on. When this rule is enabled, ASCII decoding is also enabled to enforce correct functioning. UAG715 User's Guide 331