HP 6125XLG R2306-HP 6125XLG Blade Switch Security Configuration Guide - Page 195
Configuring uRPF, uRPF check modes, uRPF operation
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 195 highlights
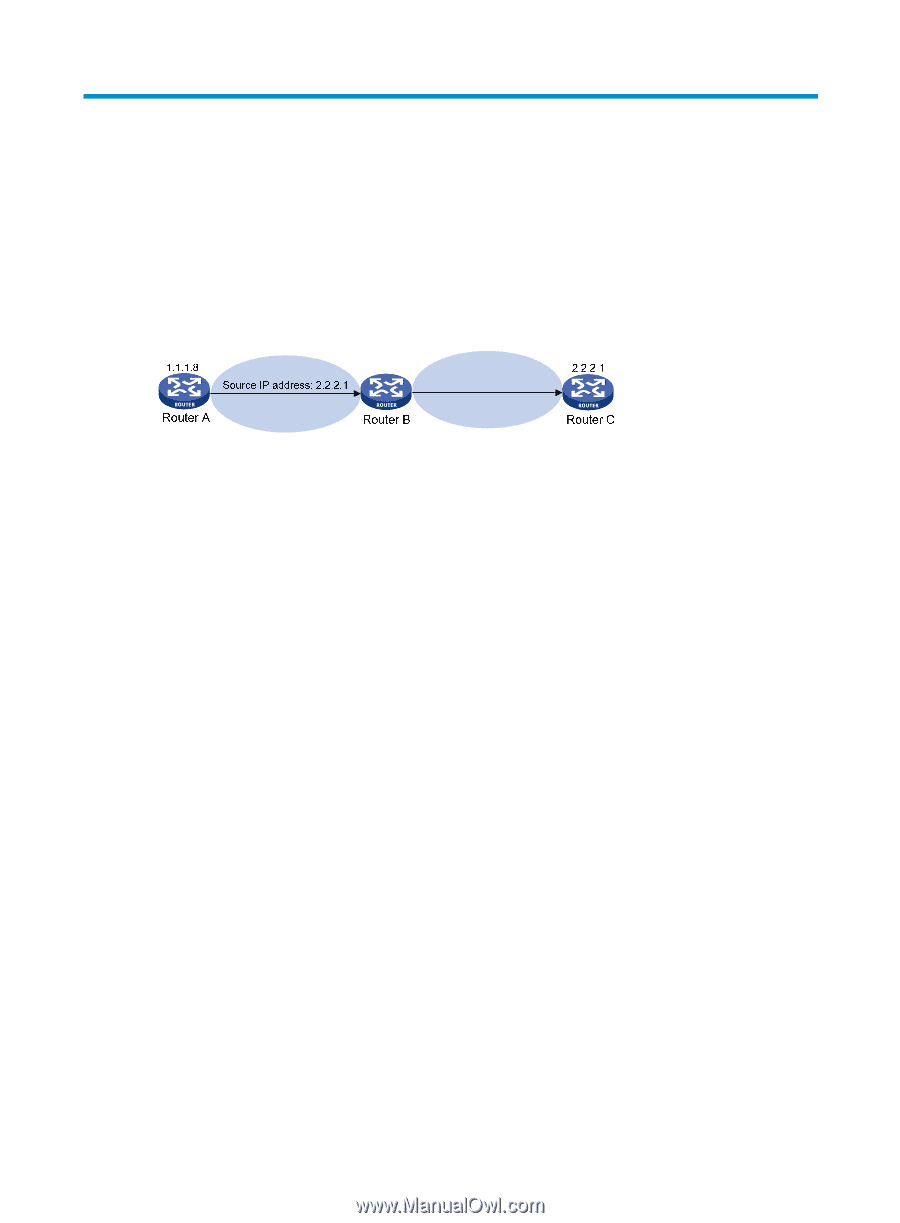
Configuring uRPF Unicast Reverse Path Forwarding (uRPF) protects a network against source address spoofing attacks, such as DoS and DDoS attacks. Attackers send packets with a forged source address to access a system that uses IP-based authentication, in the name of authorized users or even the administrator. Even if the attackers or other hosts cannot receive any response packets, the attacks are still disruptive to the attacked target. Figure 66 Source address spoofing attack As shown in Figure 66, an attacker on Router A sends the server (Router B) requests with a forged source IP address 2.2.2.1 at a high rate, and Router B sends response packets to IP address 2.2.2.1 (Router C). Consequently, both Router B and Router C are attacked. If the administrator disconnects Router C by mistake, the network service is interrupted. Attackers can also send packets with different forged source addresses or attack multiple servers simultaneously to block connections or even break down the network. uRPF can prevent these source address spoofing attacks. It checks whether an interface that receives a packet is the output interface of the FIB entry that matches the source address of the packet. If not, uRPF considers it a spoofing attack and discards the packet. uRPF check modes uRPF supports strict and loose modes. Strict uRPF check-To pass strict uRPF check, the source address of a packet and the receiving interface must match the destination address and output interface of a FIB entry. In some scenarios (such as asymmetrical routing where the interface receiving upstream traffic is different from the interface forwarding downstream traffic), strict uRPF might discard valid packets. Strict uRPF is often deployed between a PE and a CE. Loose uRPF check-To pass loose uRPF check, the source address of a packet must match the destination address of a FIB entry. Loose uRPF can avoid discarding valid packets, but might let go attack packets. Loose uRPF is often deployed between ISPs, especially in asymmetrical routing. uRPF operation Figure 67 shows how uRPF works. 186