HP 6125XLG R2306-HP 6125XLG Blade Switch Security Configuration Guide - Page 227
Verifying the configuration, Configuring an IKE-based IPsec tunnel for IPv4 packets, Network
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 227 highlights
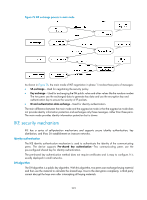
[SwitchB-ipsec-policy-manual-use1-10] sa string-key inbound esp simple abcdefg [SwitchB-ipsec-policy-manual-use1-10] quit # Apply the IPsec policy use1 to interface VLAN-interface 1. [SwitchB] interface vlan-interface 1 [SwitchB-Vlan-interface1] ipsec policy use1 Verifying the configuration After the previous configurations, an IPsec tunnel between Switch A and Switch B is established, and the traffic between the switches is IPsec protected. Use the display ipsec sa command to display IPsec SAs on Switch A and Switch B. This example uses Switch A. [SwitchA] display ipsec sa Interface: Vlan-interface 1 IPsec policy: map1 Sequence number: 10 Mode: manual Tunnel id: 549 Encapsulation mode: tunnel Path MTU: 1443 Tunnel: local address: 2.2.2.1 remote address: 2.2.3.1 Flow: as defined in ACL 3101 [Inbound ESP SA] SPI: 54321 (0x0000d431) Transform set: ESP-ENCRYPT-AES-CBC-192 ESP-AUTH-SHA1 No duration limit for this SA [Outbound ESP SA] SPI: 12345 (0x00003039) Transform set: ESP-ENCRYPT-AES-CBC-192 ESP-AUTH-SHA1 No duration limit for this SA Configuring an IKE-based IPsec tunnel for IPv4 packets Network requirements As shown in Figure 74, establish an IPsec tunnel between Switch A and Switch B to protect data flows between the switches. Configure the IPsec tunnel as follows: • Specify the encapsulation mode as tunnel, the security protocol as ESP, the encryption algorithm as AES-CBC-192, and the authentication algorithm as HMAC-SHA1. • Set up SAs through IKE negotiation. 218