HP 6125XLG R2306-HP 6125XLG Blade Switch Security Configuration Guide - Page 21
AAA methods, Fundamentals, Configuration Guide
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 21 highlights
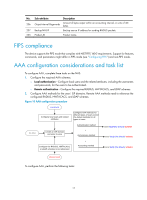
AAA methods AAA supports configuring different authentication, authorization, and accounting methods for different types of users in an ISP domain. The NAS determines the ISP domain and access type of a user, and uses the methods configured for the access type in the domain to control the user's access. AAA also supports configuring a set of default methods for an ISP domain. These default methods are used for users for whom no specific AAA methods are configured. The device supports the following authentication methods: • No authentication-This method trusts all users and does not perform authentication. For security purposes, do not use this method. • Local authentication-The NAS authenticates users by itself, based on the locally configured user information including the usernames, passwords, and attributes. Local authentication allows high speed and low cost, but the amount of information that can be stored is limited by the size of the storage space. • Remote authentication-The NAS works with a RADIUS, HWTACACS, or LDAP server to authenticate users. Remote authentication provides centralized information management, high capacity, high reliability, and support for centralized authentication service for multiple NASs. You can configure backup methods to be used when the remote server is not available. The device supports the following authorization methods: • No authorization-The NAS performs no authorization exchange. After passing authentication, non-login users can access the network, FTP users are authorized access to the root directory of the NAS but cannot access it, and login users only obtain the default user role. • Local authorization-The NAS performs authorization according to the user attributes locally configured for users. • Remote authorization-The NAS works with a RADIUS, HWTACACS, or LDAP server to authorize users. RADIUS authorization is bound with RADIUS authentication. RADIUS authorization can work only after RADIUS authentication is successful, and the authorization information is included in the Access-Accept packet. HWTACACS authorization is separate from HWTACACS authentication, and the authorization information is included in the authorization response after successful authentication. You can configure backup methods to be used when the remote server is not available. The device supports the following accounting methods: • No accounting-The NAS does not perform accounting for the users. • Local accounting-Local accounting is implemented on the NAS. It counts and controls the number of concurrent users who use the same local user account, but does not provide statistics for charging. • Remote accounting-The NAS works with a RADIUS server or HWTACACS server for accounting. You can configure backup methods to be used when the remote server is not available. In addition, the device provides the following services for login users to enhance device security: • Command authorization-Enables the NAS to defer to the authorization server to determine whether a command entered by a login user is permitted, and allows login users to execute only authorized commands. For more information about command authorization, see Fundamentals Configuration Guide. • Command accounting-When command authorization is disabled, command accounting enables the accounting server to record all valid commands executed on the device. When command authorization is enabled, command accounting enables the accounting server to record all 12