HP 6125XLG R2306-HP 6125XLG Blade Switch Security Configuration Guide - Page 213
Mirror image ACLs, Configuring an IPsec transform set
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 213 highlights
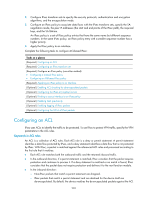
again and, if they match a permit statement, continues to process the packets. If ACL checking for de-encapsulated packets is disabled, the device directly processes the de-encapsulated packets without matching against the ACL. When defining ACL rules for IPsec, follow these guidelines: • Permit only data flows that need to be protected and use the any keyword with caution. With the any keyword specified in a permit statement, all outbound traffic matching the permit statement will be protected by IPsec and all inbound IPsec packets matching the permit statement will be received and processed, but all inbound non-IPsec packets will be dropped. This will cause all the inbound traffic that does not need IPsec protection to be dropped. • Avoid statement conflicts in the scope of IPsec policy entries. When creating a deny statement, be careful with its matching scope and matching order relative to permit statements. The policy entries in an IPsec policy have different match priorities. ACL rule conflicts between them are prone to cause mistreatment of packets. For example, when configuring a permit statement for an IPsec policy entry to protect an outbound traffic flow, you must avoid the situation that the traffic flow matches a deny statement in a higher priority IPsec policy entry. Otherwise, the packets will be sent out as normal packets. If they match a permit statement at the receiving end, they will be dropped by IPsec. Mirror image ACLs To make sure SAs can be set up and the traffic protected by IPsec can be processed correctly between two IPsec peers, create mirror image ACLs on the IPsec peers. If the ACL rules on IPsec peers do not form mirror images of each other, SAs can be set up only when both of the following requirements are met: • The range specified by an ACL rule on one peer is covered by its counterpart ACL rule on the other peer. • The peer with the narrower rule initiates SA negotiation. If a wider ACL rule is used by the SA initiator, the negotiation request might be rejected because the matching traffic is beyond the scope of the responder. Configuring an IPsec transform set An IPsec transform set, part of an IPsec policy, defines the security parameters for IPsec SA negotiation, including the security protocol, encryption algorithms, and authentication algorithms. Changes to an IPsec transform set affect only SAs negotiated after the changes. To apply the changes to existing SAs, execute the reset ipsec sa command to clear the SAs so that they can be set up by using the updated parameters. To configure an IPsec transform set: Step 1. Enter system view. 2. Create an IPsec transform set and enter its view. Command system-view ipsec transform-set transform-set-name 3. Specify the security protocol for the IPsec transform set. protocol { ah | ah-esp | esp } Remarks N/A By default, no IPsec transform set exists. Optional. By default, the IPsec transform set uses ESP as the security protocol. 204