HP 6125XLG R2306-HP 6125XLG Blade Switch Security Configuration Guide - Page 229
Specify the ESP encryption and authentication algorithms.
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 229 highlights
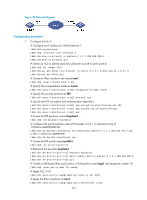
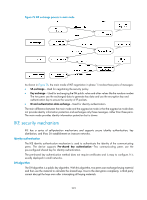
# Specify the local and remote IP addresses of the IPsec tunnel as 2.2.2.1 and 2.2.3.1. [SwitchA-ipsec-policy-isakmp-map1-10] local-address 2.2.2.1 [SwitchA-ipsec-policy-isakmp-map1-10] remote-address 2.2.3.1 # Apply the IKE profile profile1. [SwitchA-ipsec-policy-isakmp-map1-10] ike-profile profile1 [SwitchA-ipsec-policy-isakmp-map1-10] quit # Apply the IPsec policy map1 to interface VLAN-interface 1. [SwitchA] interface vlan-interface 1 [SwitchA-Vlan-interface1] ipsec policy map1 2. Configure Switch B: # Configure an IP address for VLAN-interface 1. system-view [SwitchB] interface vlan-interface 1 [SwitchB-Vlan-interface1] ip address 2.2.3.1 255.255.255.0 [SwitchB-Vlan-interface1] quit # Define an ACL to identify data flows between Switch B and Switch A. [SwitchB] acl number 3101 [SwitchB-acl-adv-3101] rule 0 permit ip source 2.2.3.1 0 destination 2.2.2.1 0 [SwitchB-acl-adv-3101] quit # Create an IPsec transform set named tran1. [SwitchB] ipsec transform-set tran1 # Specify the encapsulation mode as tunnel. [SwitchB-ipsec-transform-set-tran1] encapsulation-mode tunnel # Specify the security protocol as ESP. [SwitchB-ipsec-transform-set-tran1] protocol esp # Specify the ESP encryption and authentication algorithms. [SwitchB-ipsec-transform-set-tran1] esp encryption-algorithm aes-cbc-192 [SwitchB-ipsec-transform-set-tran1] esp authentication-algorithm sha1 [SwitchB-ipsec-transform-set-tran1] quit # Create the IKE keychain named keychain1. [SwitchB] ike keychain keychain1 # Configure the pre-shared key used with the peer 2.2.2.1 as plaintext string of 12345zxcvb!@#$%ZXCVB. [SwitchB-ike-keychain-keychain1] pre-shared-key address 2.2.2.1 255.255.255.0 key simple 12345zxcvb!@#$%ZXCVB [SwitchB-ike-keychain-keychain1] quit # Create the IKE profile named profile1. [SwitchB] ike profile profile1 # Reference the keychain keychain1. [SwitchB-ike-profile-profile1] keychain keychain1 [SwitchB-ike-profile-profile1] match remote identity address 2.2.2.1 255.255.255.0 [SwitchB-ike-profile-profile1] quit # Create an IKE mode IPsec policy entry, with the policy name use1, and sequence number 10. [SwitchB] ipsec policy use1 10 isakmp # Apply ACL 3101. 220