Netgear FS728TLP Web Management User Guide - Page 315
Port Access Entity Roles, 802.1X Sample Configuration, Authenticator, Supplicant
 |
View all Netgear FS728TLP manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 315 highlights
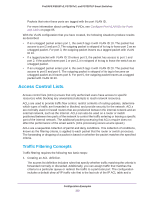
ProSAFE FS526Tv2, FS726Tv2, and FS728TLP Smart Switches The ports of an 802.1X authenticator smart switch can offer services to other systems that can be reached over the LAN. Port-based network access control allows you to control the ports of the smart switch to ensure that only systems that are authorized to access its services can do so. Access control enforces authentication of supplicants that are attached to an authenticator's controlled port. The result of the authentication process determines whether the supplicant is authorized to access services on that controlled port. Port Access Entity Roles A port access entity (PAE) can adopt one of two distinct roles within an access control interaction: • Authenticator. A port that enforces authentication before allowing access to services available through that port. • Supplicant. A port that attempts to access services offered by the authenticator. In addition, a third role exists: • Authentication server. A server that authenticates the supplicant on behalf of the authenticator. All three roles are required for an authentication exchange to be completed. The smart switch supports the authenticator role only, in which the PAE is responsible for communicating with the supplicant. The authenticator PAE also submits the information that it receives from the supplicant to the authentication server. Depending on the outcome of the RADIUS-based authentication process, the authenticator PAE sets the state of the port to authorized or unauthorized. Supplicant Authenticator switch Authentication server (RADIUS) 192.168.10.23 Supplicant Figure 17. Supplicants, authenticator, and authentication server 802.1X Sample Configuration This example shows how to configure the smart switch so that 802.1X-based authentication is required on ports e1 through e8 in a corporate conference room. These ports are available to visitors and must be authenticated before access to the network is granted. An external Configuration Examples 315