Netgear FVS338 FVS338 Reference Manual - Page 114
Extended Authentication (XAUTH) Configuration, Edge Device., IPSec Host.
 |
UPC - 606449037197
View all Netgear FVS338 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 114 highlights
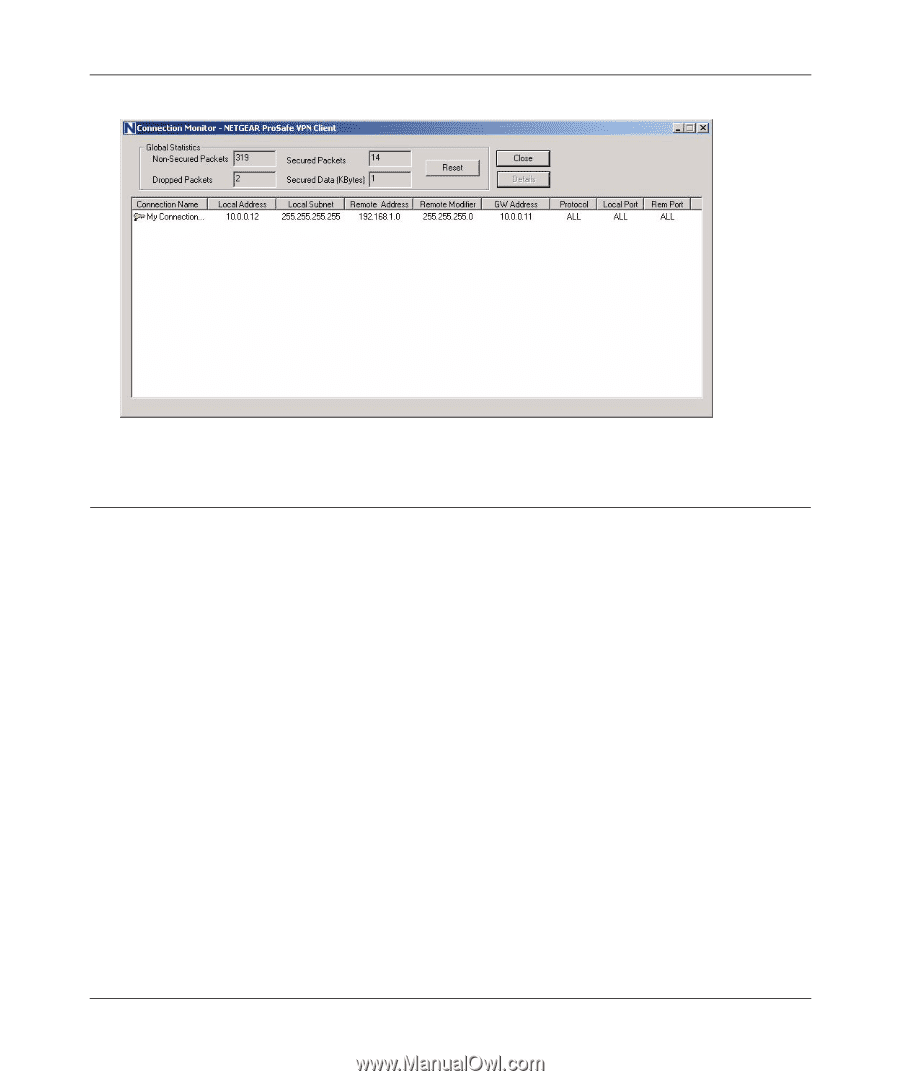
FVS338 ProSafe VPN Firewall 50 Reference Manual Figure 5-15 Extended Authentication (XAUTH) Configuration When connecting many VPN clients to a VPN gateway router, an administrator may want a unique user authentication method beyond relying on a single common preshared key for all clients. Although the administrator could configure a unique VPN policy for each user, it is more convenient for the VPN gateway router to authenticate users from a stored list of user accounts. XAUTH provides the mechanism for requesting individual authentication information from the user, and a local User Database or an external authentication server, such as a RADIUS server, provides a method for storing the authentication information centrally in the local network. XAUTH is enabled when adding or editing an IKE Policy. Two types of XAUTH are available: • Edge Device. If this is selected, the router is used as a VPN concentrator where one or more gateway tunnels terminate. If this option is chosen, you must specify the authentication type to be used in verifying credentials of the remote VPN gateways: User Database, RADIUS-PAP, or RADIUS-CHAP. • IPSec Host. If you want authentication by the remote gateway, enter a User Name and Password to be associated with this IKE policy. If this option is chosen, the remote gateway must specify the user name and password used for authenticating this gateway. 5-20 v1.0, March 2008 Virtual Private Networking