D-Link DGS-3120-24TC Product Manual - Page 238
Loopback Detection Settings, Security > Loopback Detection Settings
 |
View all D-Link DGS-3120-24TC manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 238 highlights
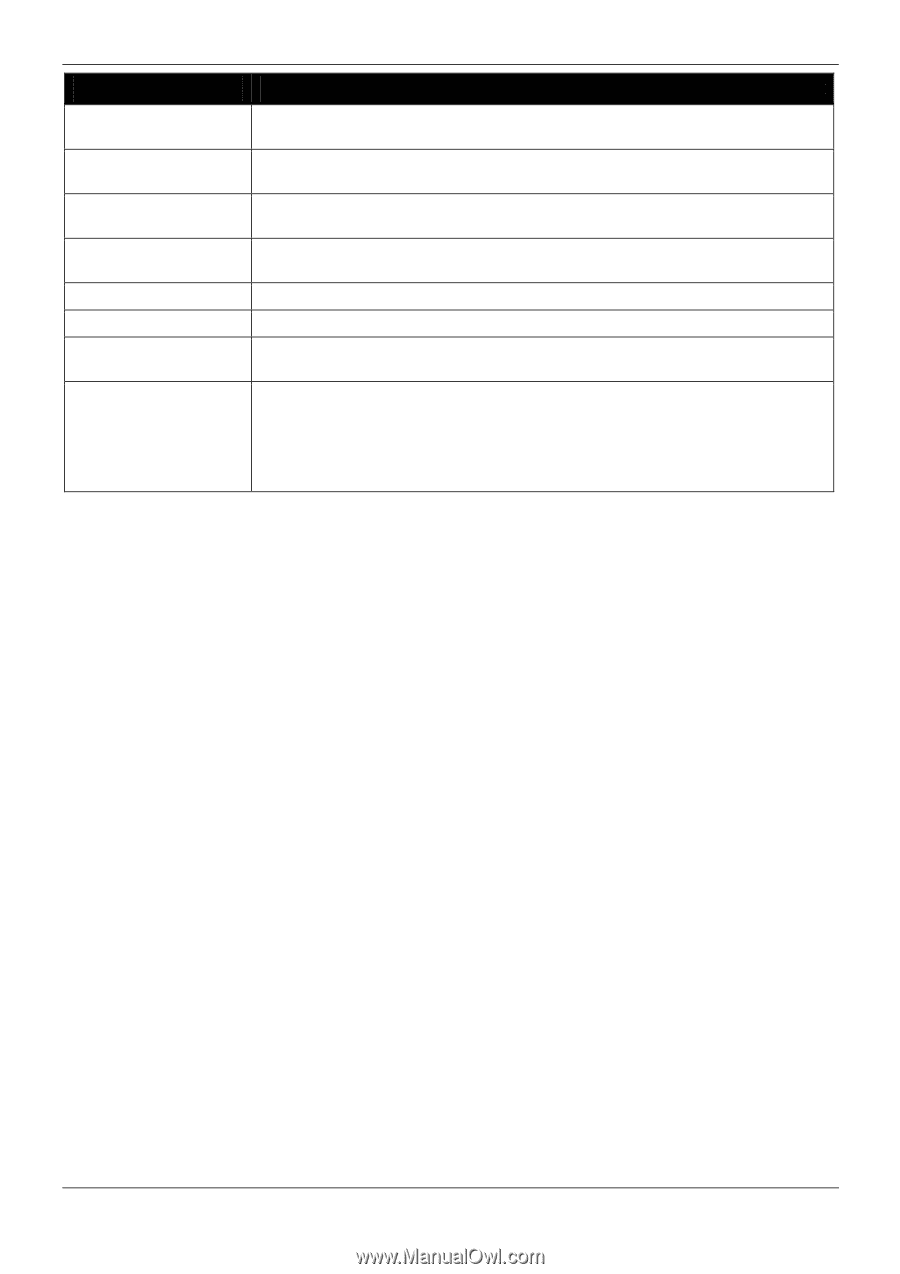
xStack® DGS-3120 Series Managed Switch Web UI Reference Guide Parameter Description BPDU Attack Protection State Click the radio buttons to enable or disable the BPDU Attack Protection state. Trap State Specify when a trap will be sent. Options to choose from are None, Attack Detected, Attack Cleared or Both. Log State Specify when a log entry will be sent. Options to choose from are None, Attack Detected, Attack Cleared or Both. Recover Time Specify the BPDU protection Auto-Recovery timer. The default value of the recovery timer is 60. Unit Select the unit you want to configure. From Port / To Port Select a range of ports to use for this configuration. State Use the drop-down menu to enable or disable the protection mode for a specific port. Mode Specify the BPDU protection mode. The default mode is shutdown. Drop - Drop all received BPDU packets when the port enters under attack state. Block - Drop all packets (include BPDU and normal packets) when the port enters under attack state. Shutdown - Shut down the port when the port enters under attack state. Click the Apply button to accept the changes made for each individual section. Loopback Detection Settings The Loopback Detection (LBD) function is used to detect the loop created by a specific port. This feature is used to temporarily shut down a port on the Switch when a CTP (Configuration Testing Protocol) packet has been looped back to the Switch. When the Switch detects CTP packets received from a port or a VLAN, this signifies a loop on the network. The Switch will automatically block the port or the VLAN and send an alert to the administrator. The Loopback Detection port will restart (change to normal state) when the Loopback Detection Recover Time times out. The Loopback Detection function can be implemented on a range of ports at a time. The user may enable or disable this function using the pull-down menu. To view this window, click Security > Loopback Detection Settings as shown below: 230