HP 6125G HP 6125G & 6125G/XG Blade Switches Security Configuration Gui - Page 177
PKI configuration examples, Certificate request from an RSA Keon CA server, Network requirements
 |
View all HP 6125G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 177 highlights
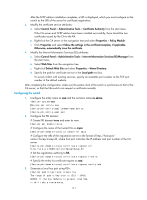
Task Display the contents or request status of a certificate. Display CRLs. Display information about certificate attribute groups. Display information about certificate attribute access control policies. Command Remarks display pki certificate { { ca | local } domain domain-name | request-status } [ | { begin | exclude | include } regular-expression ] Available in any view display pki crl domain domain-name [ | { begin | exclude Available in any view | include } regular-expression ] display pki certificate attribute-group { group-name | all } [ | { begin | exclude | include } regular-expression ] Available in any view display pki certificate access-control-policy { policy-name | all } [ | { begin | exclude | include } regular-expression ] Available in any view PKI configuration examples This section describes details about PKI configuration examples. When the CA uses Windows Server, the SCEP add-on is required, and you must use the certificate request from ra command to specify that the entity request a certificate from an RA. When the CA uses RSA Keon, the SCEP add-on is not required, and you must use the certificate request from ca command to specify that the entity request a certificate from a CA. Certificate request from an RSA Keon CA server Network requirements The switch submits a local certificate request to the CA server. The switch acquires the CRLs for certificate verification. Figure 46 Network diagram Configuring the CA server 1. Create a CA server named myca: In this example, you need to configure these basic attributes on the CA server at first: { Nickname-Name of the trusted CA. { Subject DN-DN information of the CA, including the Common Name (CN), Organization Unit (OU), Organization (O), and Country (C). Use the default values for the other attributes. 167