HP 6125G HP 6125G & 6125G/XG Blade Switches Security Configuration Gui - Page 252
Configuration procedure, Configuring ARP packet validity check
 |
View all HP 6125G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 252 highlights
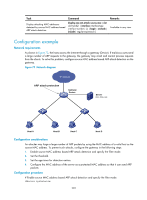
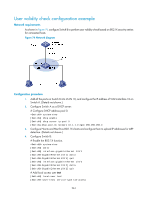
• At least the configured rules, static IP source guard binding entries, DHCP snooping entries, or 802.1X security entries must be available for user validity check. Otherwise, ARP packets received from ARP untrusted ports will be discarded, except the ARP packets with an OUI MAC address as the sender MAC address when voice VLAN is enabled. • You must specify a VLAN for an IP source guard binding entry. Otherwise, no ARP packets can match the IP source guard binding entry. Configuration procedure To configure user validity check: Step 1. Enter system view. 2. Set rules for user validity check. 3. Enter VLAN view. Command system-view arp detection id-number { permit | deny } ip { any | ip-address [ ip-address-mask ] } mac { any | mac-address [ mac-address-mask ] } [ vlan vlan-id ] vlan vlan-id 4. Enable ARP detection for the VLAN. arp detection enable 5. Return to system view. quit 6. Enter Layer 2 Ethernet interface/Layer 2 aggregate interface interface-type interface view. interface-number 7. Configure the port as a trusted port on which ARP detection does not apply. arp detection trust Remarks N/A Optional. By default, no rule is configured. N/A ARP detection based on static IP source guard binding entries/DHCP snooping entries/802.1X security entries/OUI MAC addresses is disabled by default. N/A N/A Optional. The port is an untrusted port by default. Configuring ARP packet validity check Perform this task to enable validity check for ARP packets received on untrusted ports and specify the following objects to be checked. • src-mac-Checks whether the sender MAC address in the message body is identical to the source MAC address in the Ethernet header. If they are identical, the packet is forwarded. Otherwise, the packet is discarded. • dst-mac-Checks the target MAC address of ARP replies. If the target MAC address is all-zero, all-one, or inconsistent with the destination MAC address in the Ethernet header, the packet is considered invalid and discarded. • ip-Checks the sender and target IP addresses of ARP replies, and the sender IP address of ARP requests. All-zero, all-one, or multicast IP addresses are considered invalid and the corresponding packets are discarded. To configure ARP packet validity check: 242