HP 6125G HP 6125G & 6125G/XG Blade Switches Security Configuration Gui - Page 79
Access device as the initiator, 802.1X authentication procedures
 |
View all HP 6125G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 79 highlights
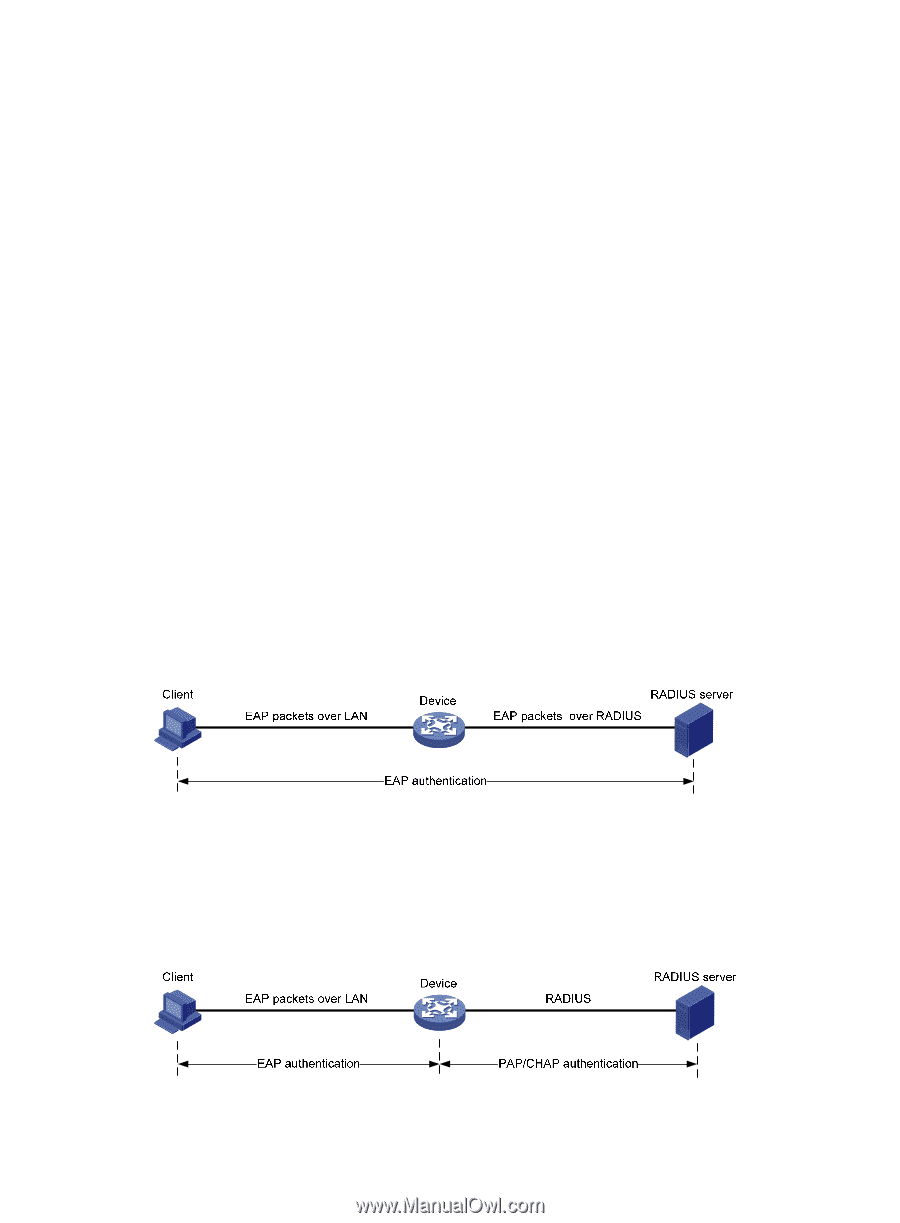
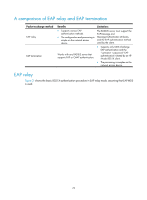
the authentication server does not support the multicast address, you must use an 802.1X client, the HP iNode 802.1X client for example, that can send broadcast EAPOL-Start packets. Access device as the initiator The access device initiates authentication, if a client, the 802.1X client available with Windows XP for example, cannot send EAPOL-Start packets. The access device supports the following modes: • Multicast trigger mode-The access device multicasts Identity EAP-Request packets periodically (every 30 seconds by default) to initiate 802.1X authentication. • Unicast trigger mode-Upon receiving a frame with the source MAC address not in the MAC address table, the access device sends an Identity EAP-Request packet out of the receiving port to the unknown MAC address. It retransmits the packet if no response has been received within a certain time interval. 802.1X authentication procedures 802.1X authentication has two approaches: EAP relay and EAP termination. You choose either mode depending on the support of the RADIUS server for EAP packets and EAP authentication methods. • EAP relay mode EAP relay is defined in IEEE 802.1X. In this mode, the network device uses EAPoR packets to send authentication information to the RADIUS server, as shown in Figure 29. In EAP relay mode, the client must use the same authentication method as the RADIUS server. On the network access device, you only need to execute the dot1x authentication-method eap command to enable EAP relay. Figure 29 EAP relay • EAP termination mode In EAP termination mode, the network access device terminates the EAP packets received from the client, encapsulates the client authentication information in standard RADIUS packets, and uses (Password Authentication Protocol) PAP or (Password Authentication Protocol) CHAP to authenticate to the RADIUS server, as shown in Figure 30. Figure 30 EAP termination 69