HP 6125XLG R2306-HP 6125XLG Blade Switch Network Management and Monitoring Com - Page 97
write-view, notify-view, Security model, keyword for the group, Security key settings, for the user
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 97 highlights
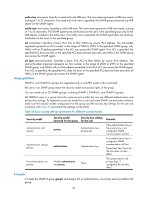
write-view view-name: Specifies a read and write MIB view. The view-name represents a MIB view name, a string of 1 to 32 characters. If no read and write view is specified, the SNMP group cannot set any MIB object on the SNMP agent. notify-view view-name: Specifies a notify MIB view. The view-name represents a MIB view name, a string of 1 to 32 characters. The SNMP agent sends notifications to the users in the specified group only for the MIB objects included in the notify view. If no notify view is specified, the SNMP agent does not send any notification to the users in the specified group. acl acl-number: Specifies a basic IPv4 ACL to filter NMSs by source IPv4 address. The acl-number argument represents an ACL number in the range of 2000 to 2999. In the specified SNMP group, only NMSs with an IP address permitted in the ACL can access the SNMP agent. If no ACL is specified, the specified ACL does not exist, or the specified ACL does not have any rules, any NMS in the SNMP group can access the SNMP agent. acl ipv6 ipv6-acl-number: Specifies a basic IPv6 ACL to filter NMSs by source IPv6 address. The ipv6-acl-number argument represents an ACL number in the range of 2000 to 2999. In the specified SNMP group, only NMSs with an IPv6 address permitted in the IPv6 ACL can access the SNMP agent. If no ACL is specified, the specified ACL does not exist, or the specified ACL does not have any rules, all NMSs in the SNMP group can access the SNMP agent. Usage guidelines SNMPv1 and SNMPv2c groups are supported only in non-FIPS mode in this command. All users in an SNMP group share the security model and access rights of the group. You can create up to 20 SNMP groups, including SNMPv1, SNMPv2c, and SNMPv3 groups. All SNMPv3 users in a group share the same security model, but can use different authentication and privacy key settings. To implement a security model for a user and avoid SNMP communication failures, make sure the security model configuration for the group and the security key settings for the user are compliant with Table 25 and match the settings on the NMS. Table 25 Basic security setting requirements for different security models Security model Authentication with privacy Authentication without privacy No authentication, no privacy Security model Security key settings keyword for the group for the user privacy Authentication key, privacy key authentication Authentication key Neither authentication nor privacy None Remarks If the authentication key or the privacy key is not configured, SNMP communication will fail. If no authentication key is configured, SNMP communication will fail. The privacy key (if any) for the user does not take effect. The authentication and privacy keys, if configured, do not take effect. Examples # Create the SNMPv3 group group1 and assigns the no authentication, no privacy security model to the group. 95