HP 6125XLG R2306-HP 6125XLG Blade Switch Network Management and Monitoring Con - Page 26
Enable NTP, as a trusted
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 26 highlights
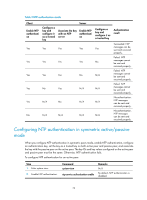
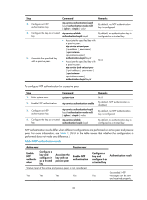
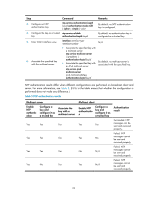
Step Command Remarks 3. Configure an NTP authentication key. ntp-service authentication-keyid keyid authentication-mode md5 { cipher | simple } value By default, no NTP authentication key is configured. 4. Configure the key as a trusted ntp-service reliable key. authentication-keyid keyid By default, no authentication key is configured as a trusted key. 5. Associate the specified key with a passive peer. • Associate the specified key with a passive peer: ntp-service unicast-peer { ip-address | peer-name } [ vpn-instance vpn-instance-name ] authentication-keyid keyid • Associate the specified key with N/A a passive peer: ntp-service ipv6 unicast-peer { ipv6-address | peer-name } [ vpn-instance vpn-instance-name ] authentication-keyid keyid To configure NTP authentication for a passive peer: Step 1. Enter system view. Command system-view 2. Enable NTP authentication. ntp-service authentication enable 3. Configure an NTP authentication key. ntp-service authentication-keyid keyid authentication-mode md5 { cipher | simple } value 4. Configure the key as a trusted ntp-service reliable key. authentication-keyid keyid Remarks N/A By default, NTP authentication is disabled. By default, no NTP authentication key is configured. By default, no authentication key is configured as a trusted key. NTP authentication results differ when different configurations are performed on active peer and passive peer. For more information, see Table 3. (N/A in the table means that whether the configuration is performed does not make any difference.) Table 3 NTP authentication results Active peer Passive peer Enable NTP authentic ation Configure a key and configure it as a trusted key Associate the key with an passive peer Enable NTP authentication Stratum level of the active and passive peers is not considered. Yes Yes Yes Yes Configure a key and configure it as a trusted key Authentication result Succeeded. NTP Yes messages can be sent and received properly. 20