D-Link DGS-1510-28P User Manual - Page 353
DoS Attack Prevention Settings, Security > DoS Attack Prevention Settings
 |
View all D-Link DGS-1510-28P manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 353 highlights
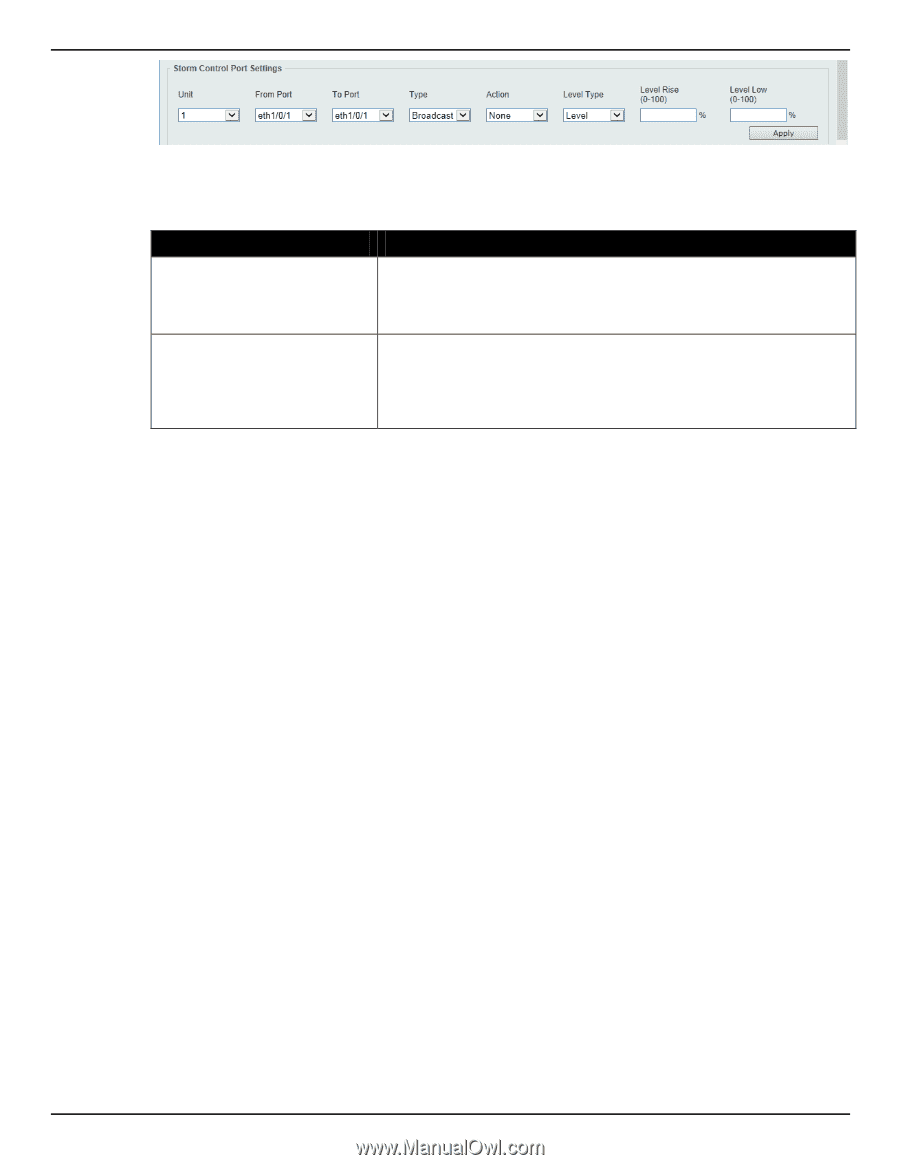
DGS-1510 Series Gigabit Ethernet SmartPro Switch Web UI Reference Guide Figure 9-85 Storm Control (Level) window The fields that can be configured are described below: Parameter Level Rise Level Low Description Enter the rise level value used here. This option specifies the rise threshold value as a percentage of the total bandwidth per port at which traffic is received on the port. This value must be between 0% and 100%. Enter the low level value used here. This option specifies the low threshold value as a percentage of the total bandwidth per port at which traffic is received on the port. This value must be between 0% and 100%. If the low level is not specified, the default value is 80% of the specified risen level. Click the Apply button to accept the changes made. DoS Attack Prevention Settings This window is used to view and configure the Denial-of-Service (DoS) attack prevention settings. The following well-known DoS types which can be detected by most switches: • Land Attack: This type of attack involves IP packets where the source and destination address are set to the address of the target device. It may cause the target device to reply to itself continuously. • Blat Attack: This type of attack will send packets with the TCP/UDP source port equal to the destination port of the target device. It may cause the target device to respond to itself. • TCP-Null: This type of attack involves port scanning by using specific packets which contain a sequence number of 0 and no flags. • TCP-Xmas: This type of attack involves port scanning by using specific packets which contain a sequence number of 0 and the Urgent (URG), Push (PSH), and FIN flags. • TCP SYN-FIN: This type of attack involves port scanning by using specific packets which contain SYN and FIN flags. • TCP SYN SrcPort Less 1024: This type of attack involves port scanning by using specific packets which contain source port 0 to 1023 and SYN flag. • Ping of Death Attack: A ping of death is a type of attack on a computer that involves sending a malformed or otherwise a malicious ping to a computer. A ping is normally 64 bytes in size (many computers cannot handle a ping larger than the maximum IP packet size) which is 65535 bytes. The sending of a ping of this size can crash the target computer. Traditionally, this bug has been relatively easy to exploit. Generally, sending a 65536 byte ping packet is illegal according to networking protocol, but a packet of such a size can be sent if it is fragmented; when the target computer reassembles the packet, a buffer overflow can occur, which often causes a system crash. • TCP Tiny Fragment Attack: The Tiny TCP Fragment attacker uses IP fragmentation to create extremely small fragments and force the TCP header information into a separate packet fragment to pass through the check function of the router and issue an attack. • All Types: All of above types. To view the following window, click Security > DoS Attack Prevention Settings, as shown below: 345