Netgear M4100-50G CLI Manual - Page 581
capture {file|remote|line}
 |
View all Netgear M4100-50G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 581 highlights
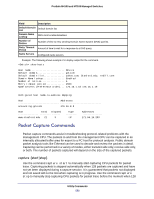
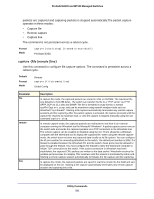
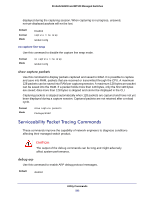
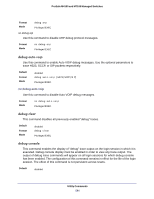
ProSafe M4100 and M7100 Managed Switches packets are captured and capturing packets is stopped automatically.The packet capture operates in three modes: • Capture file • Remote capture • Capture line The command is not persistent across a reboot cycle. Format Mode capture {start|stop} {transmit|receive|all} Privileged EXEC capture {file|remote|line} Use this command to configure file capture options. The command is persistent across a reboot cycle. Default Format Mode Remote capture {file|remote|line} Global Config Parameter file remote line Description In capture file mode, the captured packets are stored in a file on NVRAM. The maximum file size defaults to 524,288 bytes. The switch can transfer the file to a TFTP server via TFTP, SFTP, SCP via CLI, web and SNMP. The file is formatted in pcap format, is named cpuPktCapture.pcap, and can be examined using network analyzer tools such as Wireshark® by Ethereal®. Starting a file capture automatically terminates any remote capture sessions and line capturing. After the packet capture is activated, the capture proceeds until the capture file reaches its maximum size, or until the capture is stopped manually using the CLI command capture stop. In remote capture mode, the captured packets are redirected in real time to an external computer running the Wireshark tool for Microsoft® Windows®. A packet capture server runs on the switch side and sends the captured packets via a TCP connection to the Wireshark tool. The remote capture can be enabled or disabled using the CLI. There should be a Windows computer with the Wireshark tool to display the captured file. When using the remote capture mode, the switch does not store any captured data locally on its file system. You can configure the IP port number for connecting Wireshark to the switch. The default port number is 2002. If a firewall is installed between the Wireshark PC and the switch, these ports must be allowed to pass through the firewall. You must configure the firewall to allow the Wireshark computer to initiate TCP connections to the switch. If the socket connection to Wireshark has been established, the captured CPU packets are written to the data socket. Wireshark receives the packets and processes it to display. This continues until the session is terminated by either end. Starting a remote capture session automatically terminates the file capture and line capturing. In capture line mode, the captured packets are saved in real-time mode into the RAM and can be displayed on the CLI. Starting a line capture automatically terminates any remote capture session and capturing into a file. Utility Commands 581