3Com 8760 User Guide - Page 172
X Authentication, authentication is then verified by a RADIUS server using EAP Extensible
 |
UPC - 662705506531
View all 3Com 8760 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 172 highlights
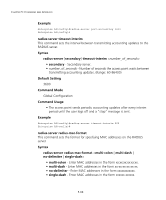
CHAPTER 5: COMMAND LINE INTERFACE Example Enterprise AP#show radius Radius Server Information IP : 0.0.0.0 Port : 1812 Key : ***** Retransmit : 3 Timeout : 5 Radius MAC format : no-delimiter Radius VLAN format : HEX Radius Secondary Server Information IP : 0.0.0.0 Port : 1812 Key : ***** Retransmit : 3 Timeout : 5 Radius MAC format : no-delimiter Radius VLAN format : HEX Enterprise AP# 802.1X Authentication The access point supports IEEE 802.1X access control for wireless clients. This control feature prevents unauthorized access to the network by requiring an 802.1X client application to submit user credentials for authentication. Client authentication is then verified by a RADIUS server using EAP (Extensible Authentication Protocol) before the access point grants client access to the network. The 802.1X EAP packets are also used to pass dynamic unicast session keys and static broadcast keys to wireless clients. Table 20 802.1X Authentication Command 802.1x 802.1x broadcast-keyrefresh-rate 802.1x session-keyrefresh-rate 802.1x session-timeout Function Mode Page Configures 802.1X as disabled, supported, or required IC-W-VAP 5-71 Sets the interval at which the primary broadcast keys IC-W-VAP 5-72 are refreshed for stations using 802.1X dynamic keying Sets the interval at which unicast session keys are IC-W-VAP 5-73 refreshed for associated stations using dynamic keying Sets the timeout after which a connected client must be IC-W-VAP 5-73 re-authenticated 5-70