D-Link DGS-3627G Product Manual - Page 420
Compound Authentication, Any MAC, 802.1X or WAC Mode
 |
UPC - 790069293764
View all D-Link DGS-3627G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 420 highlights
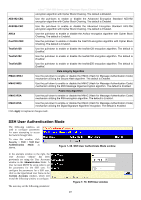
Parameter xStack® DGS-3600 Series Layer 3 Managed Gigabit Ethernet Switch Description User Name Enter a User Name of no more than 15 characters to identify the SSH user. This User Name must be a previously configured user account on the Switch. Auth. Mode The administrator may choose one of the following to set the authorization for users attempting to access the Switch. Host Based - This parameter should be chosen to use a remote SSH server for authentication purposes. Choosing this parameter requires the user to input the following information to identify the SSH user. Host Name - Displays an alphanumeric string of no more than 31 characters to identify the remote SSH user. Host IP - Displays the corresponding IP address of the SSH user. Password - This parameter should be chosen to use an administrator-defined password for authentication. Upon entry of this parameter, the Switch will prompt the administrator for a password, and then to re-type the password for confirmation. Public Key - This parameter should be chosen to use the publickey on a SSH server for authentication. Host Name Enter an alphanumeric string of no more than 32 characters to identify the remote SSH user. This parameter is only used in conjunction with the Host Based choice in the Auth. Mode field. Host IP Enter the corresponding IP address of the SSH user. This parameter is only used in conjunction with the Host Based choice in the Auth. Mode field. Click Apply to implement changes made. NOTE: To set the SSH User Authentication parameters on the Switch, a User Account must be previously configured. For more information on configuring local User Accounts on the Switch, see the User Accounts section of this manual located in the Administration section. Compound Authentication Modern networks employ many authentication methods. The Compound Authentication methods supported by this Switch include 802.1X, MAC-based Access Control (MAC), Web-based Access Control (WAC), Japan Web-based Access Control (JWAC), and IP-MAC-Port Binding (IMPB). The Compound Authentication feature allows clients running different authentication methods to connect to the network using the same switch port. The Compound Authentication feature can be implemented using one of the following modes: Any (MAC, 802.1X or WAC) Mode In the diagram on the right, the Switch port has been configured to allow clients to authenticate using 802.1X, MAC, or WAC. When a client tries to connect to the network, the Switch will try to authenticate the client using one of these methods and if the client passes, it will be granted access to the network. Figure 7- 71. Any Mode example 404