Dell Force10 MXL Blade MXL 10/40GbE Switch IO Module Configuration Guide - Page 181
DHCP Snooping, Enable DCHP Snooping
 |
View all Dell Force10 MXL Blade manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 181 highlights
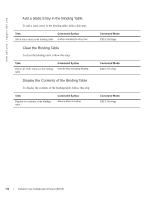
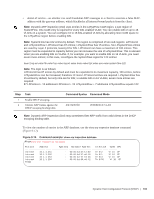
DHCP Snooping DHCP snooping protects networks from spoofing. In the context of DHCP snooping, all ports are either trusted or untrusted. By default, all ports are untrusted. Trusted ports are ports through which attackers cannot connect. Manually configure ports connected to legitimate servers and relay agents as trusted. When you enable DHCP snooping, the relay agent builds a binding table-using DHCPACK messages- containing the client MAC address, IP addresses, IP address lease time, port, VLAN ID, and binding type. Every time the relay agent receives a DHCPACK on an trusted port, it adds an entry to the table. The relay agent then checks all subsequent DHCP client-originated IP traffic (DHCPRELEASE, DHCPNACK, and DHCPDECLINE) against the binding table to ensure that the MAC-IP address pair is legitimate, and that the packet arrived on the correct port. Packets that do not pass this check are dropped. This check-point prevents an attacker from spoofing a client and declining or releasing the real client's address. Server-originated packets (DHCPOFFER, DHCPACK, DHCPNACK) that arrive on an untrusted port are also dropped. This check-point prevents an attacker from impostering as a DHCP server to facilitate a man-in-the-middle (MITM) attack. Binding table entries are deleted when a lease expires, or the relay agent encounters a DHCPRELEASE, DHCPNACK, DHCPDECLINE. FTOS Behavior: Introduced in FTOS version 7.8.1.0, DHCP snooping was available for Layer 3 only and dependent on DHCP relay agent (ip helper-address). FTOS version 8.2.1.0 extends DHCP snooping to Layer 2. You do not have to enable relay agent to snoop on Layer 2 interfaces. FTOS Behavior: Binding table entries are deleted when a lease expires or when the relay agent encounters a DHCPRELEASE. The switch maintains a list of snooped VLANs. When the binding table is exhausted, DHCP packets are dropped on snooped VLANs, while these packets are forwarded across non-snooped VLANs. Because DHCP packets are dropped, no new IP address assignments are made. However, DHCPRELEASE and DHCPDECLINE packets are allowed so that the DHCP snooping table can decrease in size. After the table usage falls below the maximum limit of 4000 entries, new IP address assignments are allowed. Note: DHCP server packets are dropped on all untrusted interfaces of a system configured for DHCP snooping. To prevent these packets from being dropped, configure ip dhcp snooping trust on the server-connected port. Enable DCHP Snooping To enable DCHP snooping, follow these steps: Step 1 2 3 Task Enable DHCP snooping globally. Specify ports connected to DHCP servers as trusted. Enable DHCP snooping on a VLAN. Command Syntax ip dhcp snooping ip dhcp snooping trust ip dhcp snooping vlan Command Mode CONFIGURATION INTERFACE CONFIGURATION Dynamic Host Configuration Protocol (DHCP) | 179