Dell Force10 MXL Blade MXL 10/40GbE Switch IO Module Configuration Guide - Page 184
Dynamic ARP Inspection, Command example
 |
View all Dell Force10 MXL Blade manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 184 highlights
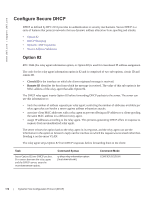
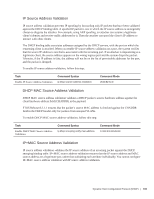
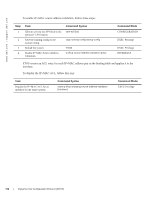
www.dell.com | support.dell.com To view the number of entries in the table, use the show ip dhcp snooping binding command. This output displays the snooping binding table created using the ACK packets from the trusted port (Figure 9-11). Figure 9-11. Command example: show ip dhcp snooping binding FTOS#show ip dhcp snooping binding Codes : S - Static D - Dynamic IP Address MAC Address Expires(Sec) Type VLAN Interface 10.1.1.251 00:00:4d:57:f2:50 172800 D Vl 10 Te 0/2 10.1.1.252 00:00:4d:57:e6:f6 172800 D Vl 10 Te 0/1 10.1.1.253 00:00:4d:57:f8:e8 172740 D Vl 10 Te 0/3 10.1.1.254 00:00:4d:69:e8:f2 172740 D Vl 10 Te 0/50 Total number of Entries in the table : 4 Dynamic ARP Inspection Dynamic address resolution protocol (ARP) inspection prevents ARP spoofing by forwarding only ARP frames that have been validated against the DHCP binding table. ARP is a stateless protocol that provides no authentication mechanism. Network devices accepts ARP request and replies from any device. ARP replies are accepted even when no request was sent. If a client receives an ARP message for which a relevant entry already exists in its ARP cache, it overwrites the existing entry with the new information. The lack of authentication in ARP makes it vulnerable to spoofing. ARP spoofing is a technique attackers use to inject false IP to MAC mappings into the ARP cache of a network device. It is used to launch man-in-the-middle (MITM), and denial-of-service (DoS) attacks, among others. A spoofed ARP message is one in which the MAC address in the sender hardware address field and the IP address in the sender protocol field are strategically chosen by the attacker. For example, in an MITM attack, the attacker sends a client an ARP message containing the attacker's MAC address and the gateway's IP address. The client then thinks that the attacker is the gateway and sends all internet-bound packets to it. Likewise, the attacker sends the gateway an ARP message containing the attacker's MAC address and the client's IP address. The gateway then thinks that the attacker is the client and forwards all packets addressed to the client to it. As a result, the attacker is able to sniff all packets to and from the client. Other attacks using ARP spoofing include: • broadcast-an attacker can broadcast an ARP reply that specifies FF:FF:FF:FF:FF:FF as the gateway's MAC address, resulting in all clients broadcasting all internet-bound packets. • MAC flooding-an attacker can send fraudulent ARP messages to the gateway until the ARP cache is exhausted, after which, traffic from the gateway is broadcast. 182 | Dynamic Host Configuration Protocol (DHCP)