Netgear GS748Tv4 GS748Tv4 Software Administration Manual - Page 176
Security, Traffic Control, Storm, Control, Ingress Control Mode, Disable, Unknown Unicast, Multicast
 |
View all Netgear GS748Tv4 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 176 highlights
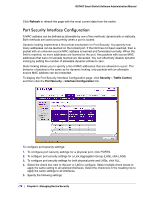
GS748T Smart Switch Software Administration Manual The switch measures the incoming broadcast/multicast/unknown unicast packet rate per port and discards packets when the rate exceeds the defined value. Storm control is enabled per interface, by defining the packet type and the rate at which the packets are transmitted. To display the Storm Control page, click Security > Traffic Control, and then click the Storm Control link. To configure storm control settings: 1. Select the check box next to the port to configure. Select multiple check boxes to apply the same setting to all selected ports. Select the check box in the heading row to apply the same settings to all ports. 2. From the Ingress Control Mode menu, select the mode of broadcast affected by storm control. • Disable. Do not use storm control. • Unknown Unicast. If the rate of unknown L2 unicast (destination lookup failure) traffic ingressing on an interface increases beyond the configured threshold, the traffic will be dropped. • Multicast. If the rate of L2 multicast traffic ingressing on an interface increases beyond the configured threshold, the traffic will be dropped. • Broadcast. If the rate of L2 broadcast traffic ingressing on an interface increases beyond the configured threshold, the traffic will be dropped. 3. When the selected Ingress Control Mode is an option other than Disable, select Enable or Disable from the Status menu to specify the administrative status of the mode. 4. In the Threshold field, specify the maximum rate at which unknown packets are forwarded. The range is a percent of the total threshold between 0-100%. The default is 5%. 5. Click Cancel to cancel the configuration on the screen and reset the data on the screen to the latest value of the switch. 176 | Chapter 5: Managing Device Security