ZyXEL NBG6515 User Guide - Page 219
EAP-TTLS Tunneled Transport Layer Service, PEAP Protected EAP, Dynamic WEP Key Exchange
 |
View all ZyXEL NBG6515 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 219 highlights
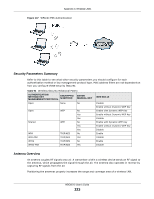
Appendix C Wireless LANs EAP-TTLS (Tunneled Transport Layer Service) EAP-TTLS is an extension of the EAP-TLS authentication that uses certificates for only the serverside authentications to establish a secure connection. Client authentication is then done by sending username and password through the secure connection, thus client identity is protected. For client authentication, EAP-TTLS supports EAP methods and legacy authentication methods such as PAP, CHAP, MS-CHAP and MS-CHAP v2. PEAP (Protected EAP) Like EAP-TTLS, server-side certificate authentication is used to establish a secure connection, then use simple username and password methods through the secured connection to authenticate the clients, thus hiding client identity. However, PEAP only supports EAP methods, such as EAP-MD5, EAP-MSCHAPv2 and EAP-GTC (EAP-Generic Token Card), for client authentication. EAP-GTC is implemented only by Cisco. LEAP LEAP (Lightweight Extensible Authentication Protocol) is a Cisco implementation of IEEE 802.1x. Dynamic WEP Key Exchange The AP maps a unique key that is generated with the RADIUS server. This key expires when the wireless connection times out, disconnects or reauthentication times out. A new WEP key is generated each time reauthentication is performed. If this feature is enabled, it is not necessary to configure a default encryption key in the wireless security configuration screen. You may still configure and store keys, but they will not be used while dynamic WEP is enabled. Note: EAP-MD5 cannot be used with Dynamic WEP Key Exchange For added security, certificate-based authentications (EAP-TLS, EAP-TTLS and PEAP) use dynamic keys for data encryption. They are often deployed in corporate environments, but for public deployment, a simple user name and password pair is more practical. The following table is a comparison of the features of authentication types. Table 93 Comparison of EAP Authentication Types EAP-MD5 EAP-TLS Mutual Authentication No Yes Certificate - Client No Yes Certificate - Server No Yes Dynamic Key Exchange No Yes Credential Integrity None Strong Deployment Difficulty Easy Hard Client Identity Protection No No EAP-TTLS Yes Optional Yes Yes Strong Moderate Yes PEAP Yes Optional Yes Yes Strong Moderate Yes LEAP Yes No No Yes Moderate Moderate No NBG6515 User's Guide 219