Dell Force10 S55T FTOS Command Line Reference Guide for the S55 System FTOS 8. - Page 222
Standard MAC ACL Commands, deny
 |
View all Dell Force10 S55T manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 222 highlights
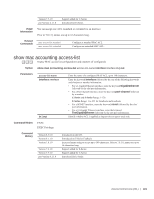
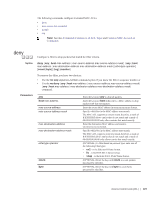
www.dell.com | support.dell.com Example Figure 7-6. Command Example: show mac accounting access-list Force10#show mac accounting access-list mac-ext interface po 1 Extended mac access-list mac-ext on GigabitEthernet 0/11 seq 5 permit host 00:00:00:00:00:11 host 00:00:00:00:00:19 count (393794576 packets) seq 10 deny host 00:00:00:00:00:21 host 00:00:00:00:00:29 count (89076777 packets) seq 15 deny host 00:00:00:00:00:31 host 00:00:00:00:00:39 count (0 packets) seq 20 deny host 00:00:00:00:00:41 host 00:00:00:00:00:49 count (0 packets) seq 25 permit any any count (0 packets) Extended mac access-list mac-ext on GigabitEthernet 0/12 seq 5 permit host 00:00:00:00:00:11 host 00:00:00:00:00:19 count (57589834 packets) seq 10 deny host 00:00:00:00:00:21 host 00:00:00:00:00:29 count (393143077 packets) seq 15 deny host 00:00:00:00:00:31 host 00:00:00:00:00:39 count (0 packets) seq 20 deny host 00:00:00:00:00:41 host 00:00:00:00:00:49 count (0 packets) seq 25 permit any any count (0 packets) Force10# Related Commands show mac accounting destination Display destination counters for Layer 2 traffic (available on physical interfaces only). Standard MAC ACL Commands When an access-list is created without any rule and then applied to an interface, ACL behavior reflects implicit permit. c and s platforms (except the S55 system) support Ingress MAC ACLs only. The supports both Ingress and Egress MAC ACLs. The following commands configure standard MAC ACLs: • deny • mac access-list standard • permit • seq Note: See also Commands Common to all ACL Types and Common MAC Access List Commands. deny c e s Configure a filter to drop packets with a the MAC address specified. Syntax deny {any | mac-source-address [mac-source-address-mask]} [count [byte]] [log] [monitor] To remove this filter, you have two choices: • Use the no seq sequence-number command syntax if you know the filter's sequence number or • Use the no deny {any | mac-source-address mac-source-address-mask} command. Parameters any mac-source-address Enter the keyword any to specify that all traffic is subject to the filter. Enter a MAC address in nn:nn:nn:nn:nn:nn format. 222 | Access Control Lists (ACL)