Dell PowerEdge M710 Web Tools Administrator’s Guide - Page 257
Transport mode and tunnel mode, Relevant RFCs
 |
View all Dell PowerEdge M710 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 257 highlights
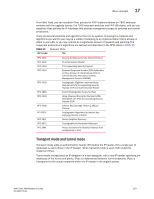
DRAFT: BROCADE CONFIDENTIAL IPsec concepts 17 From Web Tools, you can establish IPsec policies for FCIP implementations on 7800 extension switches with the upgrade license, the 7500 extension switches and FR4-18i blades, and you can establish IPsec policies for IP interfaces that provide management access to switches and control processors. There are several protocols and algorithms that can be applied. Choosing the protocols and algorithms you want to use may be a matter of adapting to an implementation that is already in place in your LAN, or you may need to do a significant amount of research and planning. The supported protocols and algorithms are defined and described in the RFCs listed in Table 19. TABLE 19 Relevant RFCs RFC number Title RFC 4301 RFC 4302 RFC 4303 RFC 4304 RFC 4305 RFC 4869 RFC 4309 RFC 4306 RF C4307 RFC 3971 RFC 3972 RFC 3041 Security Architecture for the Internet Protocol IP Authentication Header IP Encapsulating Security Payload Extended Sequence Number (ESN) Addendum to IPsec Domain of Interpretation (DOI) for Internet Security Association and Key Management Protocol (ISAKMP) Cryptographic Algorithm Implementation Requirements for Encapsulating Security Payload (ESP) and Authentication Header Suite B Cryptographic Suites for IPsec Using Advanced Encryption Standard (AES) CCM Mode with IPsec Encapsulating Security Payload (ESP) Internet Key Exchange Version 2 (IKEv2) Protocol Cryptographic Algorithms for Internet Key Exchange Version 2 (IKEv2) Secure Neighbor Discovery Cryptographically Generated Addresses Privacy Extensions for Stateless Address Auto configuration in IPv6 Transport mode and tunnel mode Transport mode adds an authentication header (AH) before the IP header. Only a single pair of addresses is used (those in the IP header). When transport mode is used, both endpoints implement IPsec. Tunnel mode encapsulates an IP datagram in a new datagram, with a new IP header specifying the addresses of the tunnel end points. IPsec is implemented between tunnel endpoints. IPsec is transparent to the actual endpoints within the IP header in the original packet. Web Tools Administrator's Guide 229 53-1001772-01