Dell PowerEdge M710 Web Tools Administrator’s Guide - Page 260
Internet Key Exchange concepts, Endpoint to Gateway, Encryption algorithms
 |
View all Dell PowerEdge M710 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 260 highlights
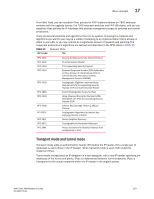
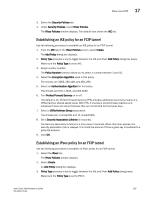
17 IPsec concepts DRAFT: BROCADE CONFIDENTIAL Endpoint to Gateway In an endpoint to gateway configuration, a protected endpoint connects through an IPsec protected tunnel. This can be used as a virtual private network (VPN) for connecting a roaming computer, like a service laptop, to a protected network. Internet Key Exchange concepts Internet Key Exchange (IKE) is used to authenticate the end points of an IP connection, and to determine security policies for IP traffic over the connection. The initiating node proposes a policy based on the following: • An encryption algorithm to protect data. • A hash algorithm to check the integrity of the authentication data. • A Pseudo-Random Function (PRF) algorithm that can be used with the hash algorithm for additional cryptographic strength. • An authentication method requiring a digital signature, and optionally a certificate exchange. • A Diffie-Hellman exchange that generates prime numbers used in establishing a shared secret key. Encryption algorithms An encryption algorithm is used to encrypt messages used in the IKE negotiation. Table 20 lists the available encryption algorithms. A brief description is provided. If you need further information, please refer to the RFC. TABLE 20 Encryption algorithm options Encryption algorithm Description RFC number 3des_cbc null_enc aes128_cbc aes256_cbc 3DES processes each block three times, using a unique 56-bit key each time. No encryption is performed. Advanced Encryption Standard (AES) 128 bit block cipher. Advanced Encryption Standard (AES) 256 bit block cipher. RFC 2451 RFC 4869 RFC 4869 232 Web Tools Administrator's Guide 53-1001772-01