HP 6125XLG R2306-HP 6125XLG Blade Switch Fundamentals Configuration Guide - Page 64
Verifying the configuration, RBAC configuration example for HWTACACS authentication users
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 64 highlights
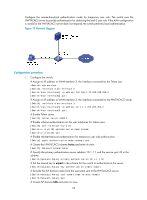
[Switch-role-role2-ifpolicy] quit [Switch-role-role2] quit 2. Configure the RADIUS server: # Add either of the user role attributes to the dictionary file of the FreeRADIUS server. Cisco-AVPair = "shell:roles=\"role2\"" Cisco-AVPair = "shell:roles*\"role2\"" # Configure the settings required for the FreeRADIUS server to communicate with the switch. (Details not shown.) Verifying the configuration # Telnet to the switch, and enter the username and password to access the user interface. (Details not shown.) # Verify that you can use all commands available in ISP view. system-view [Switch] domain abc [Switch-isp-abc] authentication login radius-scheme abc [Switch-isp-abc] quit # Verify that you can use all read and write commands of the features radius and arp. Take radius as an example. [Switch] radius scheme rad [Switch-radius-rad] primary authentication 2.2.2.2 [Switch-radius-rad] display radius scheme rad ... Output of the RADIUS scheme is omitted. # Verify that you cannot configure any VLAN except VLANs 1 to 20. Take VLAN 10 and VLAN 30 as examples. [Switch] vlan 10 [Switch-vlan10] quit [Switch] vlan 30 Permission denied. # Verify that you cannot configure any interface except Ten-GigabitEthernet 1/1/5 to Ten-GigabitEthernet 1/1/10. Take Ten-GigabitEthernet 1/1/6 and Ten-GigabitEthernet 1/1/12 as examples. [Switch] vlan 10 [Switch-vlan10] port ten-gigabitethernet 1/1/6 [Switch-vlan10] port ten-gigabitethernet 1/1/12 Permission denied. RBAC configuration example for HWTACACS authentication users Unless otherwise noted, devices in the configuration example are operating in non-FIPS mode. Network requirements The switch in Figure 18 uses local authentication for login users, including the Telnet user at 192.168.1.58. This Telnet user uses the username test@bbb and is assigned the user role level-0. 57