Cisco RV042 User Guide - Page 46
Manual, Phase 2 SA Life Time - router mode
 |
UPC - 745883560530
View all Cisco RV042 manuals
Add to My Manuals
Save this manual to your list of manuals |
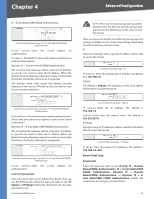
Page 46 highlights
Chapter 4 Advanced Configuration a one-way hashing algorithm that produces a 128-bit digest. SHA is a one-way hashing algorithm that produces a 160-bit digest. SHA is recommended because it is more secure. Make sure both ends of the VPN tunnel use the same authentication method. Phase 1 SA Life Time Configure the length of time a VPN tunnel is active in Phase 1. The default value is 28800 seconds. Perfect Forward Secrecy If the Perfect Forward Secrecy (PFS) feature is enabled, IKE Phase 2 negotiation will generate new key material for IP traffic encryption and authentication, so hackers using brute force to break encryption keys will not be able to obtain future IPSec keys. Phase 2 DH Group If the Perfect Forward Secrecy feature is disabled, then no new keys will be generated, so you do not need to set the Phase 2 DH Group (the key for Phase 2 will match the key in Phase 1). There are three groups of different prime key lengths. Group 1 is 768 bits, and Group 2 is 1,024 bits. Group 5 is 1,536 bits. If network speed is preferred, select Group 1. If network security is preferred, select Group 5. You do not have to use the same DH Group that you used for Phase 1. Phase 2 Encryption Phase 2 is used to create one or more IPSec SAs, which are then used to key IPSec sessions. Select a method of encryption: NULL, DES (56-bit), 3DES (168-bit), AES-128 (128-bit), AES-192 (192-bit), or AES256 (256-bit). It determines the length of the key used to encrypt or decrypt ESP packets. AES-256 is recommended because it is the most secure. Both ends of the VPN tunnel must use the same Phase 2 Encryption setting. Phase 2 Authentication Select a method of authentication, NULL, MD5, or SHA. The authentication method determines how the ESP packets are validated. MD5 is a one-way hashing algorithm that produces a 128-bit digest. SHA is a one-way hashing algorithm that produces a 160-bit digest. SHA is recommended because it is more secure. Both ends of the VPN tunnel must use the same Phase 2 Authentication setting. Phase 2 SA Life Time Configure the length of time a VPN tunnel is active in Phase 2. The default is 3600 seconds. Preshared Key This specifies the pre-shared key used to authenticate the remote IKE peer. Enter a key of keyboard and hexadecimal characters, e.g., My_@123 or 4d795f40313233. This field allows a maximum of 30 characters and/or hexadecimal values. Both ends of the VPN tunnel must use the same Preshared Key. It is strongly recommended that you change the Preshared Key periodically to maximize VPN security. 10/100 4-Port VPN Router Manual If you select Manual, you generate the key yourself, and no key negotiation is needed. Manual key management is used in small static environments or for troubleshooting purposes. Keying Mode > Manual Incoming and Outgoing SPI (Security Parameter Index) SPI is carried in the ESP (Encapsulating Security Payload Protocol) header and enables the receiver and sender to select the SA, under which a packet should be processed. Hexadecimal values is acceptable, and the valid range is 100~ffffffff. Each tunnel must have a unique Incoming SPI and Outgoing SPI. No two tunnels share the same SPI. The Incoming SPI here must match the Outgoing SPI value at the other end of the tunnel, and vice versa. Encryption Select a method of encryption, DES or 3DES. This determines the length of the key used to encrypt or decrypt ESP packets. DES is 56-bit encryption and 3DES is 168-bit encryption. 3DES is recommended because it is more secure. Make sure both ends of the VPN tunnel use the same encryption method. Authentication Select a method of authentication, MD5 or SHA1. The Authentication method determines how the ESP packets are validated. MD5 is a one-way hashing algorithm that produces a 128-bit digest. SHA is a one-way hashing algorithm that produces a 160-bit digest. SHA1 is recommended because it is more secure. Make sure both ends of the VPN tunnel use the same authentication method. Encryption Key This field specifies a key used to encrypt and decrypt IP traffic. Enter a key of hexadecimal values. If DES is selected, the Encryption Key is 16-bit, which requires 16 hexadecimal values. If you do not enter enough hexadecimal values, then the rest of the Encryption Key will be automatically completed with zeroes, so the Encryption Key will be 16-bit. If 3DES is selected, the Encryption Key is 48-bit, which requires 40 hexadecimal values. If you do not enter enough hexadecimal values, then the rest of the Encryption Key will be automatically completed with zeroes, so the Encryption Key will be 48bit. Make sure both ends of the VPN tunnel use the same Encryption Key. Authentication Key This field specifies a key used to authenticate IP traffic. Enter a key of hexadecimal values. 39