Cisco AIR-LAP1252AG-A-K9 Software Configuration Guide - Page 126
Combining MAC-Based, EAP, and Open Authentication, Authenticating Client Devices
 |
UPC - 882658140716
View all Cisco AIR-LAP1252AG-A-K9 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 126 highlights
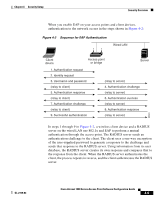
Security Overview Chapter 4 Security Setup During shared key authentication, the access point sends an unencrypted challenge text string to any device attempting to communicate with the access point. The device requesting authentication encrypts the challenge text and sends it back to the access point. If the challenge text is encrypted correctly, the access point allows the requesting device to authenticate. Both the unencrypted challenge and the encrypted challenge can be monitored, however, which leaves the access point open to attack from an intruder who calculates the WEP key by comparing the unencrypted and encrypted text strings. Because of this weakness, shared key authentication can be less secure than open authentication. Like open authentication, shared key authentication does not rely on a RADIUS server on your network. Figure 4-5 shows the authentication sequence between a device trying to authenticate and an access point using shared key authentication. In this example the device's WEP key matches the access point's key, so it can authenticate and communicate. Figure 4-5 Sequence for Shared Key Authentication Access point or bridge with WEP key = 123 1. Authentication request 2. Unencrypted challenge 3. Encrypted challenge response 4. Authentication response Client device with WEP key = 123 54584 Combining MAC-Based, EAP, and Open Authentication You can set up the access point to authenticate client devices using a combination of MAC-based and EAP authentication. When you enable this feature, client devices that associate to the access point using 802.11 open authentication first attempt MAC authentication; if MAC authentication succeeds, the client device joins the network. If MAC authentication fails, the access point waits for the client device to attempt EAP authentication. See the "Authenticating Client Devices Using MAC Addresses or EAP" section on page 4-34 for more information on this feature. Cisco Aironet 1200 Series Access Point Software Configuration Guide 4-8 OL-2159-03