Dell PowerConnect W-IAP92 Dell Instant 6.1.3.4-3.1.0.0 User Guide - Page 167
Table 27, Table 26
 |
View all Dell PowerConnect W-IAP92 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 167 highlights
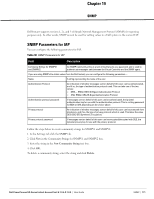
Table 26 Infrastructure Detection Policies (Continued) Detection Level Detection Policy High Detect AP Impersonation Detect Adhoc Networks Detect Valid SSID Misuse Detect Wireless Bridge Detect 802.11 40MHz intolerance settings Detect Active 802.11n Greenfield Mode Detect AP Flood Attack Detect Client Flood Attack Detect Bad WEP Detect CTS Rate Anomaly Detect RTS Rate Anomaly Detect Invalid Address Combination Detect Malformed Frame- HT IE Detect Malformed Frame- Association Request Detect Malformed Frame- Auth Detect Overflow IE Detect Overflow EAPOL Key Detect Beacon Wrong Channel Detect devices with invalid MAC OUI The following table describes the detection policies that are enabled in Client Detection Custom settings field. Table 27 Client Detection Policies Detection Level Off Low Medium High Detection Policy All detection policies are disabled. Detect Valid Station Mis association Detect Disconnect Station Attack Detect Omerta Attack Detect FATA-Jack Attack Detect Block ACK DOS Detect Hotspotter Attack Detect unencrypted Valid Client Detect Power Save DOS Attack Detect EAP Rate Anomaly Detect Rate Anomaly Detect Chop Chop Attack Detect TKIP Replay Attack IDS Signature- Air Jack IDS Signature- ASLEAP Dell PowerConnect W-Series Instant Access Point 6.1.3.4-3.1.0.0 | User Guide Intrusion Detection System | 167