Dell PowerConnect W Clearpass 100 Software 3.9 Deployment Guide - Page 148
Creating a Server Certificate and Self-Signed Certificate Authority
 |
View all Dell PowerConnect W Clearpass 100 Software manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 148 highlights
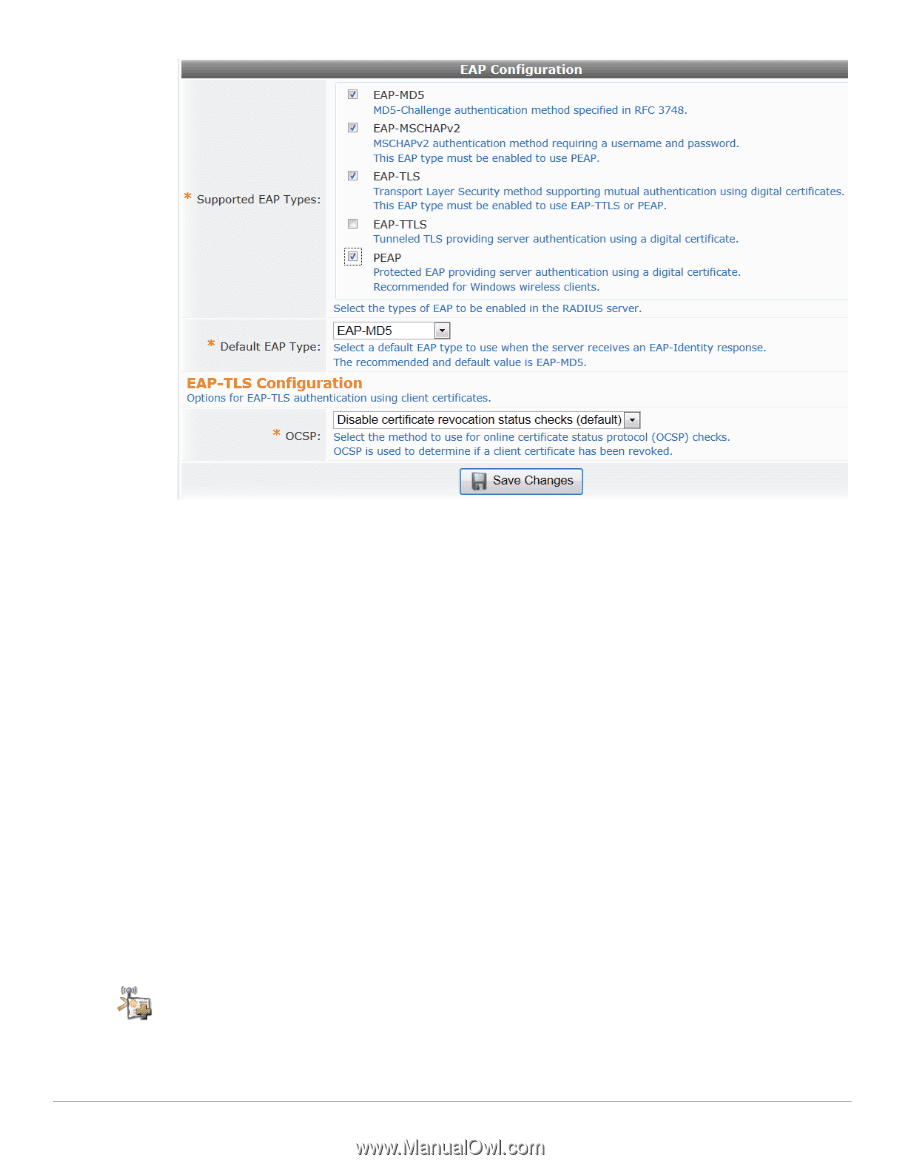
2. In the Supported EAP Types row, mark the check box for each type the RADIUS server should support. The available types are EAP-MD5, EAP-MSCHAPv2, EAP-TLS, EAP-TTLS, and PEAP. If you select EAP-TLS, the EAP-TLS Configuration area is added at the bottom of the form. 3. In the Default EAP Type row, use the drop-down list to select the EAP type to use as the default when the server receives an EAP-Identity response. 4. If you selected EAP-TLS as one of the supported types, use the EAP-TLS Configuration area to configure status checks for client certificates. In the drop-down list in the OCSP row, select one of the following options: Disable certificate revocation status checks (default)-If this option is selected, no OCSP checks are made to determine the client certificate's revocation status. Automatically check certificate revocation status-If this option is selected, an OCSP responder defined in the client certificate is used to obtain revocation status. If no OCSP responder is defined in the client certificate, then the local certificate authority is used to check status. Manually specify OCSP URL for certificate checks-If this option is selected, the URL specified in the OCSP row of the EAP Configuration form is used to verify revocation status, and any OCSP responder defined in the client certificate is ignored. The "Manually specify OCSP URL for certificate checks" option adds the OCSP Responder row to the form. 5. If you chose the manual option for certificate checks, in the OCSP Responder row, enter the URL of the service to be used to check certificate status. 6. Click the Save Changes button. Creating a Server Certificate and Self-Signed Certificate Authority To create a new server certificate and self-signed certificate authority (CA), go to RADIUS > Authentication > EAP & 802.1X, then click the Create Server Certificate command link. The Create 148 | RADIUS Services ClearPass Guest 3.9 | Deployment Guide