Dell PowerConnect W Clearpass 100 Software 3.9 Deployment Guide - Page 79
Configuring Data Retention Policy for Certificates
 |
View all Dell PowerConnect W Clearpass 100 Software manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 79 highlights
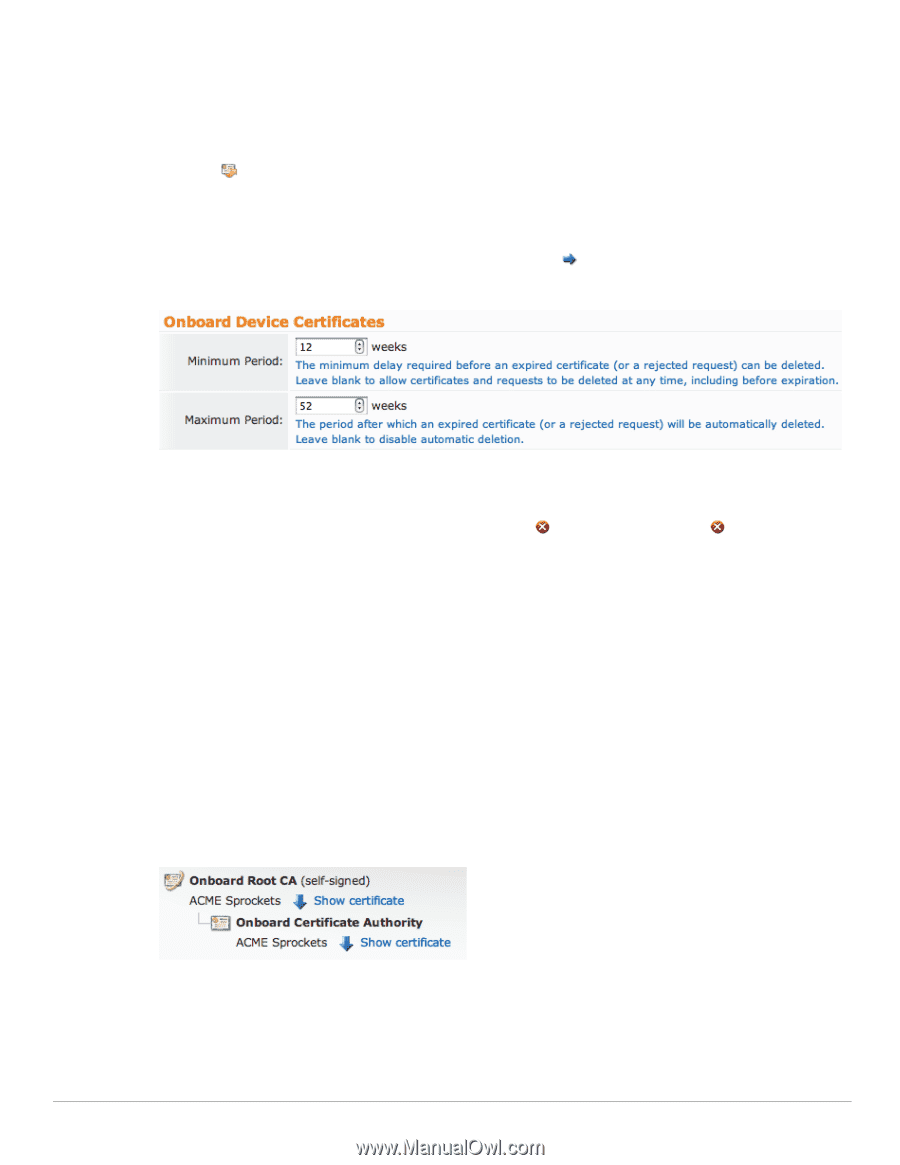
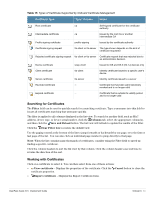
Replacement Renewal - Generates a new private key for the root certificate, and reissues the root CA certificate with an updated validity period. Use this option if the root certificate has been compromised, or if you want to invalidate all certificate that were previously issued by the CA. Whether you renew or replace the root certificate, you should distribute a new copy of the root certificate to all users of that certificate. Click the Renew Root Certificate button to perform the renewal action. Configuring Data Retention Policy for Certificates The data retention policy for certificates and certificate requests can be configured by navigating to Onboard > Certificate Authority Settings and clicking the Configure data retention link. The Manage Data Retention form is displayed. In the Onboard Device Certificates section of the form, specify a value in the Minimum Period and Maximum Period fields that is appropriate for your organization's retention policy. Note: Use a blank value for Minimum Period to enable the Delete Certificate and Delete Request actions in the Certificate Management list view. This is useful for testing and initial deployment. The default data retention policy specifies the values: Minimum Period of 12 weeks Maximum Period of 52 weeks Uploading Certificates for the Certificate Authority This page is used to view the certificate authority's current trust chain, or to upload a new certificate in the trust chain when configuring a certificate authority. Viewing the Certificate Authority's Trust Chain Navigate to Onboard > Certificate Authority Settings and click the View CA Certificate link. The Certificate Authority Trust Chain page is displayed. This page shows a graphical representation of the certificates that make up the trust chain. The first certificate listed is the root certificate. Root certificates are always self-signed and are explicitly trusted by clients. Each additional certificate shown is an intermediate certificate. The last certificate in the list is the signing certificate that is used to issue client and server certificates. ClearPass Guest 3.9 | Deployment Guide Onboard | 79