Dell Latitude CPi User Guide - Page 80
Physically Securing the Computer and the Hard-Disk Drive, Boot First Device, Boot First, Device
 |
View all Dell Latitude CPi manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 80 highlights
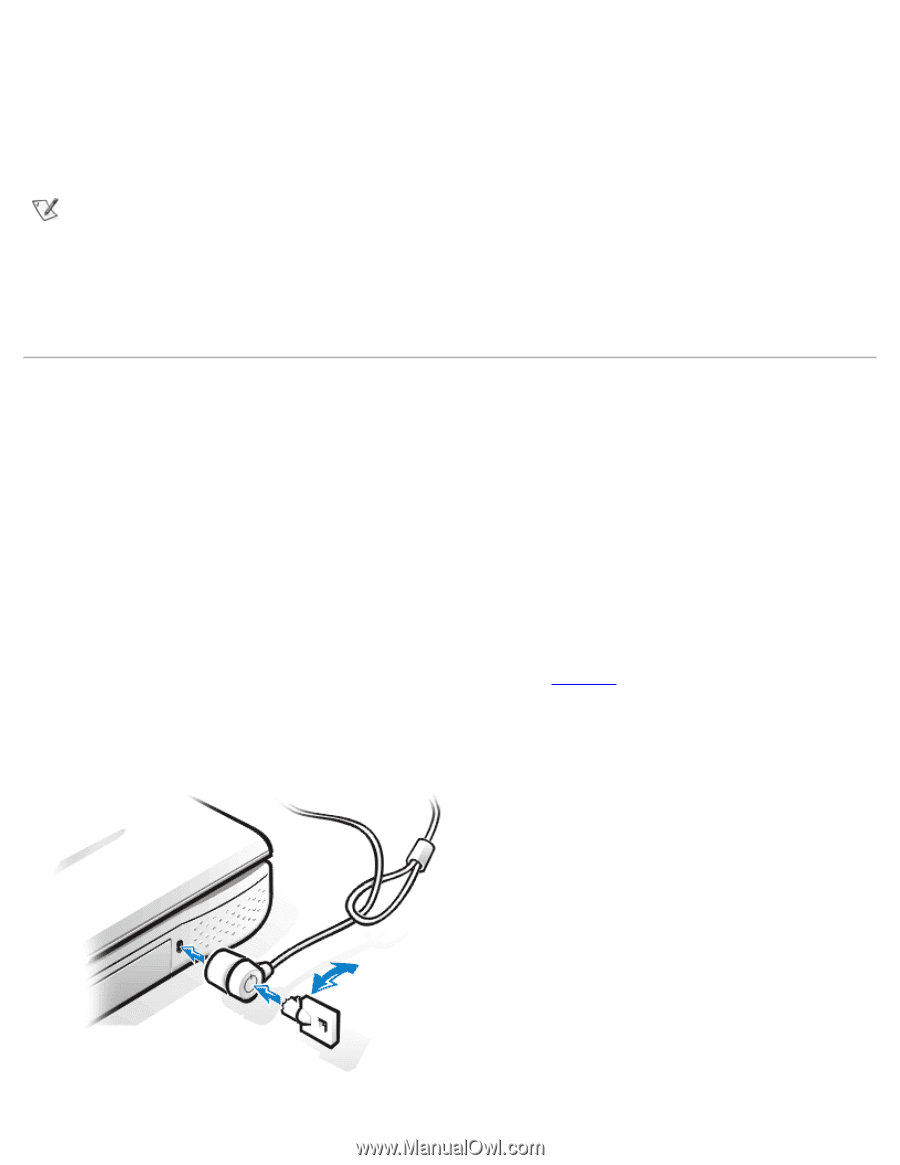
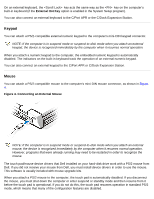
Invalid password [Press Enter to retry] If the correct password is not entered in three attempts, the computer tries to boot from another bootable device if the Boot First Device option in the System Setup program is set to allow it. If the Boot First Device option is not set to allow booting from another device, the computer returns to the state it was in when you turned it on-suspend or standby mode. NOTES: If the hard-disk drive password, the modular hard-disk drive password, and the primary password are the same, you are prompted only for the primary password. If the hard-disk drive password is different from the primary password, you are prompted for both. Two different passwords provide greater security. The administrator password provides access to the system, but it does not provide access to the hard-disk drive when it is protected by a password. Physically Securing the Computer and the Hard-Disk Drive To prevent unauthorized removal of the computer, you can use a security cable to attach the computer to an immovable object. The same mechanism can be used to lock your hard-disk drive to the computer. The security cable slot lets you attach a commercially available antitheft device to the computer and harddisk drive. Antitheft devices for portable computers usually include a segment of metal-stranded cable with an attached locking device and associated key. Complete instructions for installing this kind of antitheft device are usually included with the device. To prevent unauthorized removal of the hard-disk drive, insert the locking device into the security cable slot on the hard-disk drive panel, and lock the device with its associated key. To prevent unauthorized removal of your computer, loop the cable around an immovable object, insert the locking device into the security cable slot, and lock the device. See Figure 1 for an example of how to secure your computer. Figure 1. Securing the Computer