D-Link DWS-3160-24TC DWS-3160 Series Web UI Reference Guide - Page 246
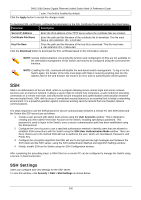
SSH Authentication Method and Algorithm Settings
 |
View all D-Link DWS-3160-24TC manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 246 highlights
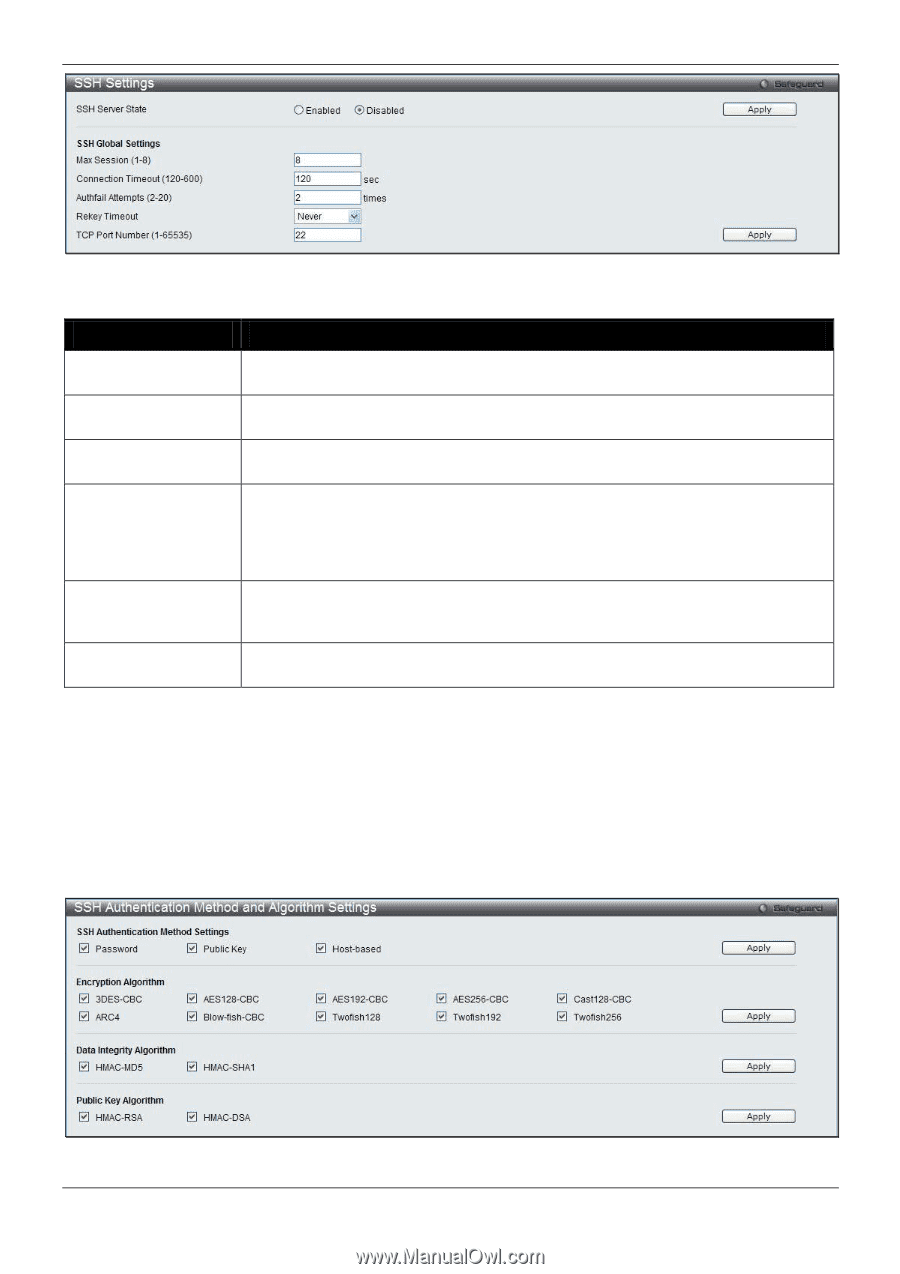
DWS-3160 Series Gigabit Ethernet Unified Switch Web UI Reference Guide Figure 11-61 SSH Settings window The fields that can be configured are described below: Parameter Description SSH Server State Use the radio buttons to enable or disable SSH on the Switch. The default is Disabled. Max. Session (1-8) Enter a value between 1 and 8 to set the number of users that may simultaneously access the Switch. The default setting is 8. Connection Timeout Allows the user to set the connection timeout. The user may set a time between 120 (120-600) and 600 seconds. The default setting is 120 seconds. Authfail Attempts (220) Allows the Administrator to set the maximum number of attempts that a user may try to log on to the SSH Server utilizing the SSH authentication. After the maximum number of attempts has been exceeded, the Switch will be disconnected and the user must reconnect to the Switch to attempt another login. The number of maximum attempts may be set between 2 and 20. The default setting is 2. Rekey Timeout This field is used to set the time period that the Switch will change the security shell encryptions by using the drop-down menu. The available options are Never, 10 min, 30 min, and 60 min. The default setting is Never. TCP Port Number (1- Here the user can enter the TCP Port Number used for SSH. The default value is 22. 65535) Click the Apply button to accept the changes made for each individual section. SSH Authentication Method and Algorithm Settings Users can configure the desired types of SSH algorithms used for authentication encryption. There are three categories of algorithms listed and specific algorithms of each may be enabled or disabled by ticking their corresponding check boxes. All algorithms are enabled by default. To view this window, click Security > SSH > SSH Authentication method and Algorithm Settings as shown below: Figure 11-62 SSH Authentication Method and Algorithm Settings window 241