Netgear M5300-52G3 Web Management User Guide - Page 520
X Example Configuration, From the 802.1X Configuration screen
 |
View all Netgear M5300-52G3 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 520 highlights
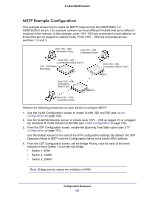
ProSafe M5300 Switch 802.1X Example Configuration This example shows how to configure the switch so that 802.1X-based authentication is required on the ports in a corporate conference room (1/0/5 - 1/0/8). These ports are available to visitors and need to be authenticated before granting access to the network. The authentication is handled by an external RADIUS server. When the visitor is successfully authenticated, traffic is automatically assigned to the guest VLAN. This example assumes that a VLAN has been configured with a VLAN ID of 150 and VLAN Name of Guest. 1. From the Port Authentication screen, select ports 1/0/5, 1/0/6, 1/0/7 and 1/0/8. 2. From the Port Control menu, select Unauthorized. The Port Control setting for all other ports where authentication is not needed should Authorized. When the Port Control setting is Authorized, the port is unconditionally put in a force-Authorized state and does not require any authentication. When the Port Control setting is Auto, the authenticator PAE sets the controlled port mode 3. In the Guest VLAN field for ports 1/0/5 - 1/0/8, enter 150 to assign these ports to the guest VLAN. You can configure additional settings to control access to the network through the ports. See Port Security Configuration on page 399 for information about the settings. 4. Click APPLY. 5. From the 802.1X Configuration screen, set the Port Based Authentication State and Guest VLAN Mode to Enable, and then click APPLY (See 802.1X Configuration on page 387). This example uses the default values for the port authentication settings, but there are several additional settings that you can configure. For example, the EAPOL Flood Mode field allows you to enable the forwarding of EAPoL frames when 802.1X is disabled on the device. 6. From the RADIUS Server Configuration screen, configure a RADIUS server with the following settings: • Server Address: 192.168.10.23 • Secret Configured: Yes • Secret: secret123 • Active: Primary For more information, see RADIUS on page 359. 7. Click ADD. 8. From the Authentication List screen, configure the default List to use RADIUS as the first authentication method (See Authentication List Configuration on page 366). This example enables 802.1X-based port security on ProSafe and prompts the hosts connected on ports g5-g8 for an 802.1X-based authentication. The switch passes the authentication information to the configured RADIUS server. Configuration Examples 520