D-Link DGS-3200-10 Product Manual - Page 161
SSH, Certificate File Name, Key File Name
 |
UPC - 790069306310
View all D-Link DGS-3200-10 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 161 highlights
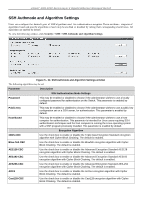
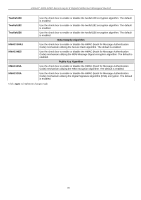
xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Certificate File Name Key File Name Enter the path and the filename of the certificate file to download. This file must have a .der extension. (Ex. c:/cert.der) Enter the path and the filename of the key file to download. This file must have a .der extension (Ex. c:/pkey.der) Click Apply to implement changes made. NOTE: Certain implementations concerning the function and configuration of SSL are not available on the web-based management of this Switch and need to be configured using the command line interface. NOTE: Enabling the SSL command will disable the web-based switch management. To log on to the Switch again, the header of the URL must begin with https://. Entering anything else into the address field of the web browser will result in an error and no authentication will be granted. SSH SSH is an ab breviation of Secure Sh ell, which is a program allowing secure remote login and secure network services over an insecure network. It allows a secure login to remote host computers, a safe method of executing commands on a remote end node, and will prov ide secure en crypted an d auth enticated commu nication b etween two n on-trusted hosts. SSH, with its array o f unmatched security features is an esse ntial tool in today's networking environment. It is a po werful guardian against numerous existing security hazards that now threaten network communications. The steps required to use the SSH protocol for secure communication between a remote PC (the SSH client) and the Switch (the SSH server) are as follows: 1. Create a user account with admin-level access using the User Accounts window (Configuration > Port Configuration > User Accounts). This is identical to creating any other admin-level User Account on the Switch, including specifying a password. This password is used to log on to the Switch, once a secure communication path has bee n established using the SSH protocol. 2. Configure the User Account to use a s pecified authorization method to identify users that are al lowed to establish SSH connections with th e Switch u sing t he SSH User Authentication Mode window. T here a re three choices as to the method SSH will use to authorize the user, which are Host Based, Password, and Public Key. 3. Configure the encryption algorithm that SSH will use to en crypt and decrypt messages sent between the SSH client and the SSH server, using the SSH Authmode and Algorithm Settings window. 4. Finally, enable SSH on the Switch using the SSH Configuration window. After completing the preceding steps, a SSH Client on a remote PC can be confi gured to manage the Switch using a secure, in band connection. 148