D-Link DGS-3200-10 Product Manual - Page 289
Appendix C - Trap Logs
 |
UPC - 790069306310
View all D-Link DGS-3200-10 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 289 highlights
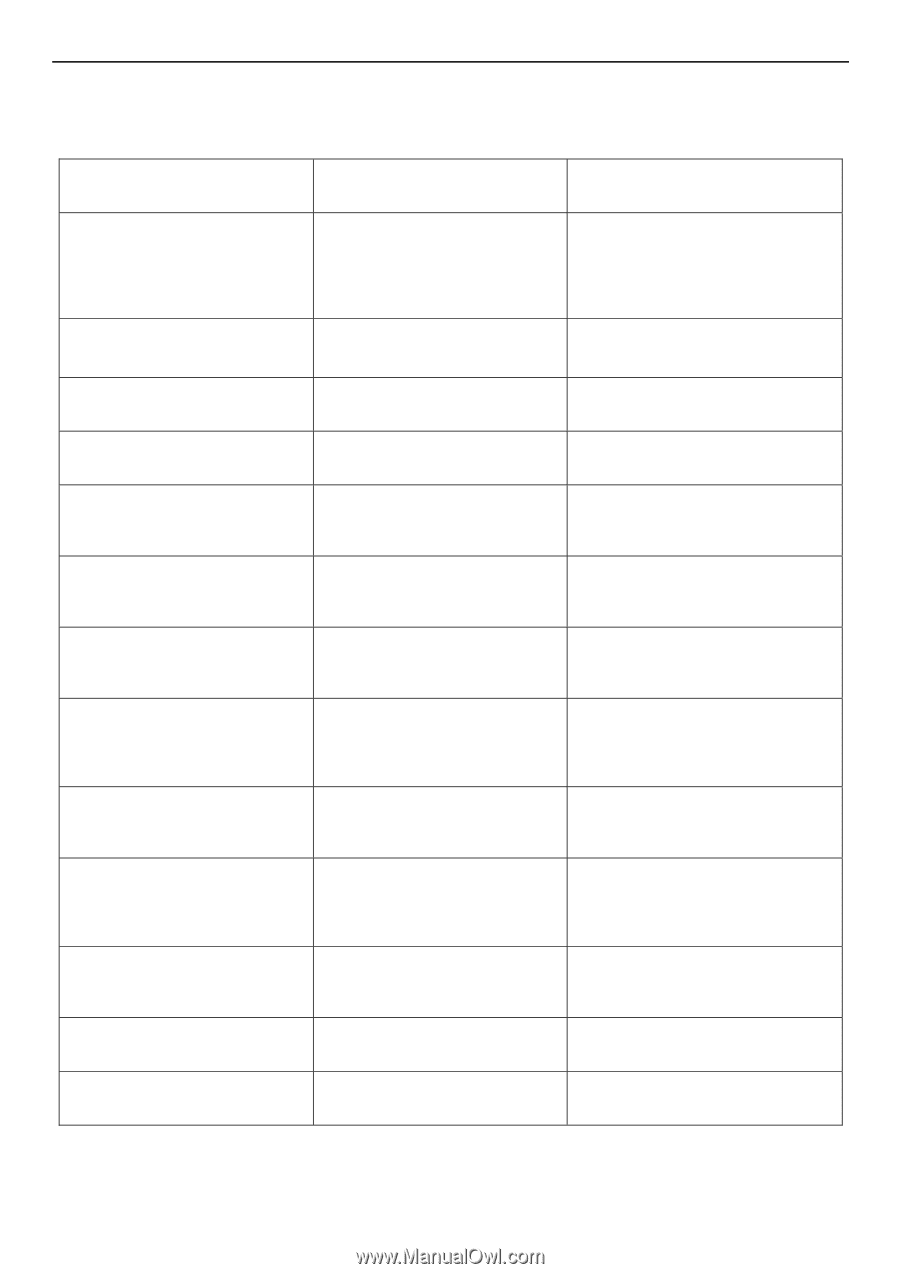
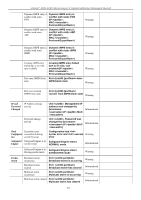
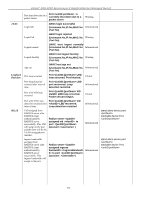
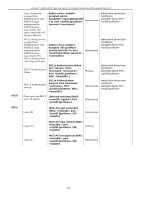
xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Appendix C - Trap Logs This table lists the trap logs found on the DGS-3200 Series Switches. MACNotificationTrap This trap indicates the MAC address 1.3.6.1.4.1.171.11.101.1.2.100.1.2.0.1 variations in the address table. PortSecurityViolationTrap When the port security trap is 1.3.6.1.4.1.171.11.101.1.2.100.1.2.0.2 enabled, new MAC addresses that violate the pre-defined port security configuration will trigger trap messages to be sent out. PortLoopOccurredTrap This trap is sent when a Port loop 1.3.6.1.4.1.171.11.101.1.2.100.1.2.0.3 occurs. PortLoopRestart VlanLoopOccurred VlanLoopRestart SafeGuardChgToExhausted SafeGuardChgToNormal PktStormOccurred PktStormCleared IpMACBindTrap MacBasedAuthLoggedSuccess MacBasedAuthLoggedFail MacBasedAuthAgesOut This trap is sent when a Port loop 1.3.6.1.4.1.171.11.101.1.2.100.1.2.0.4 restarts after the interval time. This trap is sent when a Port with a 1.3.6.1.4.1.171.11.101.1.2.100.1.2.0.5 VID loop occurs. This trap is sent when a Port with a 1.3.6.1.4.1.171.11.101.1.2.100.1.2.0.6 VID loop restarts after the interval time. This trap indicates System change 1.3.6.1.4.1.171.12.19.4.1.0.1 operation mode from normal to exhausted. This trap indicates System change 1.3.6.1.4.1.171.12.19.4.1.0.2 operation mode from exhausted to normal. This trap is sent when a packet 1.3.6.1.4.1.171.12.25.5.0.1 storm is detected by the packet storm mechanism and takes shutdown as an action. This trap is sent when the packet 1.3.6.1.4.1.171.12.25.5.0.2 storm is cleared by the packet storm mechanism. When the IP-MAC Binding trap is 1.3.6.1.4.1.171.12.23.5.0.1 enabled, if there's a new MAC that violates the pre-defined port security configuration, a trap will be sent out. This trap is sent when a MAC-based 1.3.6.1.4.1.171.12.35.11.1.0.1 access control host is successfully logged in. This trap is sent when a MAC-based 1.3.6.1.4.1.171.12.35.11.1.0.2 access control host login fails. This trap is sent when a MAC-based 1.3.6.1.4.1.171.12.35.11.1.0.3 access control host ages out. 276