D-Link DES-3528 Product Manual - Page 212
Authentication Server, Authenticator, Client
 |
UPC - 790069314346
View all D-Link DES-3528 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 212 highlights
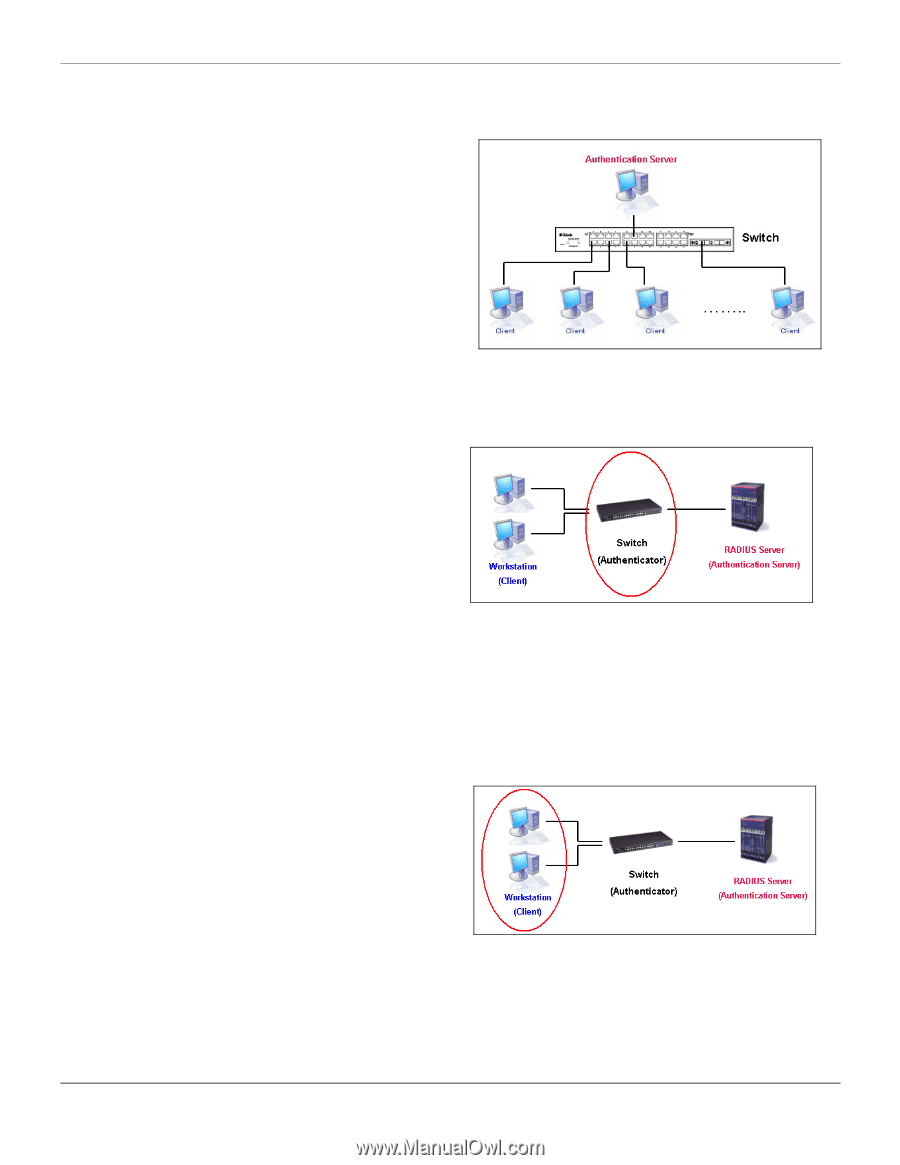
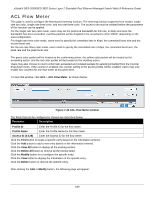
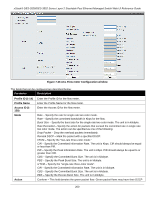
xStack® DES-3528/DES-3552 Series Layer 2 Stackable Fast Ethernet Managed Switch Web UI Reference Guide The following section will explain the three roles of Client, Authenticator and Authentication Server in greater detail. Authentication Server The Authentication Server is a remote device that is connected to the same network as the Client and Authenticator, must be running a RADIUS Server program and must be configured properly on the Authenticator (Switch). Clients connected to a port on the Switch must be authenticated by the Authentication Server (RADIUS) before attaining any services offered by the Switch on the LAN. The role of the Authentication Server is to certify the identity of the Client attempting to access the network by exchanging secure information between the RADIUS server and the Client through EAPOL packets and, in turn, informs the Switch whether or not the Client is granted access to the LAN and/or switches services. Figure 8-3 The Authentication Server Authenticator The Authenticator (the Switch) is an intermediary between the Authentication Server and the Client. The Authenticator serves two purposes when utilizing the 802.1X function. The first purpose is to request certification information from the Client through EAPOL packets, which is the only information allowed to pass through the Authenticator before access is granted to the Client. The second purpose of the Authenticator is to verify the information gathered from the Client with the Authentication Server, and to then relay that information back to the Client. Figure 8-4 The Authenticator Three steps must be implemented on the Switch to properly configure the Authenticator. 1. The 802.1X State must be Enabled. (Security / 802.1X /802.1X Settings) 2. The 802.1X settings must be implemented by port (Security / 802.1X / 802.1X Settings) 3. A RADIUS server must be configured on the Switch. (Security / 802.1X / Authentic RADIUS Server) Client The Client is simply the end station that wishes to gain access to the LAN or switch services. All end stations must be running software that is compliant with the 802.1X protocol. For users running Windows XP and Windows Vista, that software is included within the operating system. All other users are required to attain 802.1X client software from an outside source. The Client will request access to the LAN and or Switch through EAPOL packets and, in turn will respond to requests from the Switch. Figure 8-5 The Client 203