D-Link DES-3528 Product Manual - Page 278
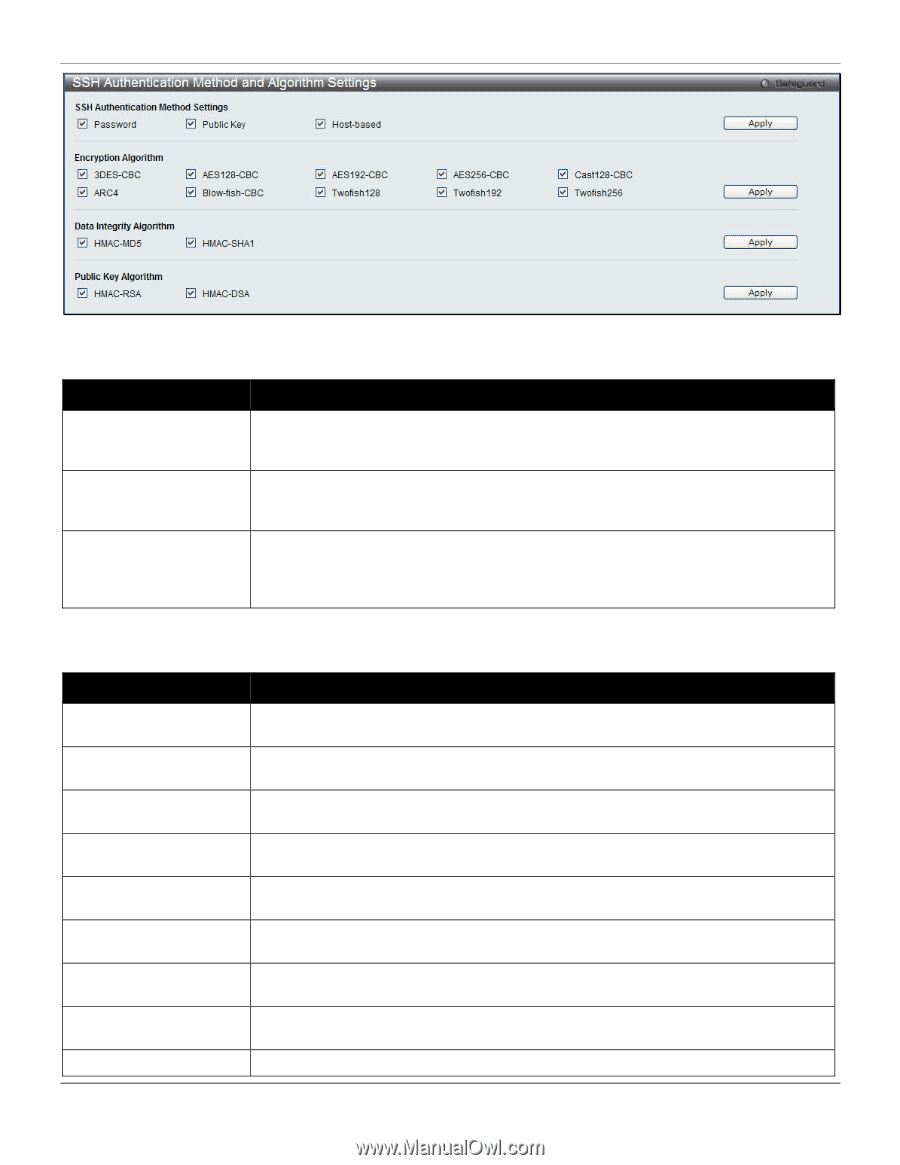
SSH Authentication Method and Algorithm Settings window, SSH Authentication Mode
 |
UPC - 790069314346
View all D-Link DES-3528 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 278 highlights
xStack® DES-3528/DES-3552 Series Layer 2 Stackable Fast Ethernet Managed Switch Web UI Reference Guide Figure 8-71 SSH Authentication Method and Algorithm Settings window The fields that can be configured for SSH Authentication Mode are described below: Parameter Description Password This may be enabled or disabled to choose if the administrator wishes to use a locally configured password for authentication on the Switch. This parameter is enabled by default. Public Key This may be enabled or disabled to choose if the administrator wishes to use a public key configuration set on a SSH server, for authentication. This parameter is enabled by default. Host-based This may be enabled or disabled to choose if the administrator wishes to use a host computer for authentication. This parameter is intended for Linux users requiring SSH authentication techniques and the host computer is running the Linux operating system with a SSH program previously installed. This parameter is enabled by default. Click the Apply button to accept the changes made. The fields that can be configured for the Encryption Algorithm are described below: Parameter Description 3DES-CBC Blow-fish CBC AES128-CBC AES192-CBC AES256-CBC ARC4 Cast128-CBC Twofish128 Twofish192 Use the check box to enable or disable the Triple Data Encryption Standard encryption algorithm with Cipher Block Chaining. The default is enabled. Use the check box to enable or disable the Blowfish encryption algorithm with Cipher Block Chaining. The default is enabled. Use the check box to enable or disable the Advanced Encryption Standard AES128 encryption algorithm with Cipher Block Chaining. The default is enabled. Use the check box to enable or disable the Advanced Encryption Standard AES192 encryption algorithm with Cipher Block Chaining. The default is enabled. Use the check box to enable or disable the Advanced Encryption Standard AES-256 encryption algorithm with Cipher Block Chaining. The default is enabled. Use the check box to enable or disable the Arcfour encryption algorithm with Cipher Block Chaining. The default is enabled. Use the check box to enable or disable the Cast128 encryption algorithm with Cipher Block Chaining. The default is enabled. Use the check box to enable or disable the twofish128 encryption algorithm. The default is enabled. Use the check box to enable or disable the twofish192 encryption algorithm. The 269