Netgear GSM7328SO Command Line Interface (CLI) User Manual - Page 159
Dynamic ARP Inspection Commands, show ip source binding
 |
UPC - 606449080162
View all Netgear GSM7328SO manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 159 highlights
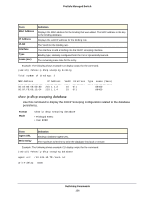
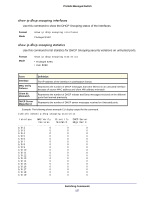
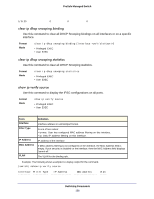
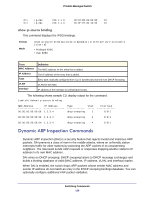
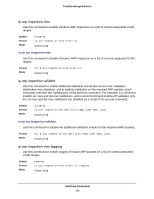
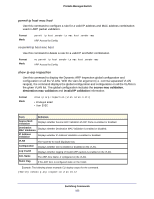
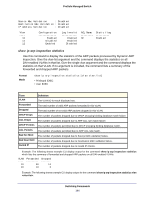
ProSafe Managed Switch 0/1 ip-mac 0/1 ip-mac 210.1.1.3 210.1.1.4 00:02:B3:06:60:80 10 00:0F:FE:00:13:04 10 show ip source binding This command displays the IPSG bindings. Format Mode show ip source binding [{static/dynamic}] [interface unit/slot/port] [vlan id] • Privileged EXEC • User EXEC Term MAC Address IP Address Type VLAN Interface Definition The MAC address for the entry that is added. The IP address of the entry that is added. Entry type; statically configured from CLI or dynamically learned from DHCP Snooping. VLAN for the entry. IP address of the interface in unit/slot/port format. The following shows sample CLI display output for the command. (switch) #show ip source binding MAC Address IP Address Type Vlan Interface 00:00:00:00:00:08 1.2.3.4 dhcp-snooping 2 1/0/1 00:00:00:00:00:09 1.2.3.4 dhcp-snooping 3 1/0/1 00:00:00:00:00:0A 1.2.3.4 dhcp-snooping 4 1/0/1 Dynamic ARP Inspection Commands Dynamic ARP Inspection (DAI) is a security feature that rejects invalid and malicious ARP packets. DAI prevents a class of man-in-the-middle attacks, where an unfriendly station intercepts traffic for other stations by poisoning the ARP caches of its unsuspecting neighbors. The miscreant sends ARP requests or responses mapping another station's IP address to its own MAC address. DAI relies on DHCP snooping. DHCP snooping listens to DHCP message exchanges and builds a binding database of valid {MAC address, IP address, VLAN, and interface} tuples. When DAI is enabled, the switch drops ARP packets whose sender MAC address and sender IP address do not match an entry in the DHCP snooping bindings database. You can optionally configure additional ARP packet validation. Switching Commands 159