Cisco MDS-9124 Troubleshooting Guide - Page 354
Unexpected User Displayed in Logs, Troubleshooting Users and Roles with Cisco ACS
 |
View all Cisco MDS-9124 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 354 highlights
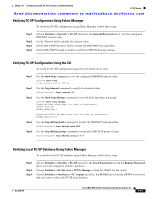
Troubleshooting Users and Roles with Cisco ACS Chapter 18 Troubleshooting Users and Roles Send documentation comments to [email protected] Unexpected User Displayed in Logs Symptom Unexpected user displayed in logs. Table 18-8 Unexpected User Displayed in Logs Symptom Unexpected user displayed in logs. Possible Cause Temporary user created by SNMP, Fabric Manager, or Device Manager. Solution Temporary users are created by Fabric Manager, Device Manager, or other applications using SNMP. This is normal behavior. These temporary users have a one hour expiration time. If you have an unexpected user with different characteristics, you should investigate that user or use the clear user CLI command to terminate that user session. Troubleshooting Users and Roles with Cisco ACS To troubleshoot user and role issues with Cisco ACS, follow these steps: Step 1 Step 2 Step 3 Choose Network Configuration using Cisco ACS and view the AAA Clients table to verify that the Cisco SAN-OS switch is configured as an AAA client on Cisco ACS. Choose User Setup > User Data Configuration to verify that the user is configured. View the Cisco IOS/PIX RADIUS Attributes setting for a user. Verify that the user is assigned the correct roles in the AV-pairs. For example, shell:roles="network-admin". Note The Cisco IOS/PIX RADIUS Attributes field is case-sensitive. Verify that the role listed in the AV-pair exists on the Cisco SAN-OS switch. Step 4 Step 5 Step 6 Step 7 If the Cisco IOS/PIX RADIUS Attributes field is not present, follow these steps: a. Choose Interface > RADIUS (Cisco IOS/PIX). b. Check the User and Group check boxes for the cisco-av-pair option and click Submit. c. Choose User Setup > User Data Configuration and add the AV-pair to assign the correct role to each user. Choose System Configuration > Logging to activate logs to look for reasons for failed authentication attempts. Choose Reports and Activity to view the resulting logs. On the Cisco SAN-OS switch, use the show radius-server command to verify that the RADIUS server timeout value is set to 5 seconds or greater. Refer to the User guide for Cisco Secure ACS at the following website for more information: http://cisco.com/en/US/products/sw/secursw/ps2086/products_user_guide_list.html 18-12 Cisco MDS 9000 Family Troubleshooting Guide, Release 3.x OL-9285-05