Cisco MDS-9124 Troubleshooting Guide - Page 356
Port Security Overview, Fabric Binding Overview, Initial Troubleshooting Checklist - port activation license
 |
View all Cisco MDS-9124 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 356 highlights
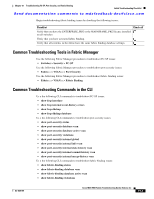
Port Security Overview Chapter 19 Troubleshooting FC-SP, Port Security, and Fabric Binding Send documentation comments to [email protected] Port Security Overview Typically, any Fibre Channel device in a SAN can attach to any SAN switch port and access SAN services based on zone membership. Port security features prevent unauthorized access to a switch port in the Cisco MDS 9000 Family: • Login requests from unauthorized Fibre Channel devices (Nx ports) and switches (xE ports) are rejected. • All intrusion attempts are reported to the SAN administrator through system messages. Fabric Binding Overview The fabric binding feature ensures ISLs are only enabled between specified switches in the fabric binding configuration. Fabric binding is configured on a per-VSAN basis. This feature helps prevent unauthorized switches from joining the fabric or disrupting current fabric operations. It uses the Exchange Fabric Membership Data (EFMD) protocol to ensure that the list of authorized switches is identical in all switches in the fabric. Domain IDs are mandatory for FICON-based fabric binding and optional for non-FICON based fabric binding. For non-FICON based fabric binding, not specifying a domain ID means that the switch with the matching WWN can login with any domain ID. Initial Troubleshooting Checklist Begin troubleshooting FC-SP issues by checking the following issues: Checklist Check off Verify licensing requirements. See Cisco MDS 9000 Family Fabric Manager Configuration Guide. Verify that your installed HBAs support FC-SP. Verify that you have configured MD5 for the hash algorithm if you are authenticating through a RADIUS or TACACS+ server. RADIUS and TACACS+ always use MD5 for CHAP authentication. Using SHA-1 as the hash algorithm may prevent RADIUS and TACACS+ usage-even if these AAA protocols are enabled for DHCHAP authentication. Verify that your AAA server is functioning properly. Begin troubleshooting port security issues by checking the following issues: Checklist Check off Verify that you have the ENTERPRISE_PKG license installed on all switches. Verify that port security is activated and that the end devices are present in the port security active database. Verify that no unauthorized devices (host or switch) are connected to a port. (One unauthorized pWWN prevents the port from being active and blocks all other devices on that port.) 19-2 Cisco MDS 9000 Family Troubleshooting Guide, Release 3.x OL-9285-05