D-Link DES-3828 Product Manual - Page 256
Access Authentication Control Commands
 |
UPC - 790069276811
View all D-Link DES-3828 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 256 highlights
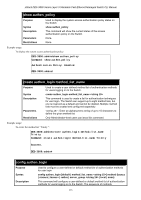
xStack DES-3800 Series Layer 3 Stackable Fast Ethernet Managed Switch CLI Manual 39 ACCESS AUTHENTICATION CONTROL COMMANDS The TACACS / XTACACS / TACACS+ / RADIUS commands let you secure access to the Switch using the TACACS / XTACACS / TACACS+ / RADIUS protocols. When a user logs in to the Switch or tries to access the administrator level privilege, he or she is prompted for a password. If TACACS / XTACACS / TACACS+ / RADIUS authentication is enabled on the Switch, it will contact a TACACS / XTACACS / TACACS+ / RADIUS server to verify the user. If the user is verified, he or she is granted access to the Switch. There are currently three versions of the TACACS security protocol, each a separate entity. The Switch's software supports the following versions of TACACS: • TACACS (Terminal Access Controller Access Control System) -Provides password checking and authentication, and notification of user actions for security purposes utilizing via one or more centralized TACACS servers, utilizing the UDP protocol for packet transmission. • Extended TACACS (XTACACS) - An extension of the TACACS protocol with the ability to provide more types of authentication requests and more types of response codes than TACACS. This protocol also uses UDP to transmit packets. • TACACS+ (Terminal Access Controller Access Control System plus) - Provides detailed access control for authentication for network devices. TACACS+ is facilitated through Authentication commands via one or more centralized servers. The TACACS+ protocol encrypts all traffic between the Switch and the TACACS+ daemon, using the TCP protocol to ensure reliable delivery. The Switch also supports the RADIUS protocol for authentication using the Access Authentication Control commands. RADIUS or Remote Authentication Dial In User Server also uses a remote server for authentication and can be responsible for receiving user connection requests, authenticating the user and returning all configuration information necessary for the client to deliver service through the user. RADIUS may be facilitated on this Switch using the commands listed in this section. In order for the TACACS / XTACACS / TACACS+ / RADIUS security function to work properly, a TACACS / XTACACS / TACACS+ / RADIUS server must be configured on a device other than the Switch, called a server host and it must include usernames and passwords for authentication. When the user is prompted by the Switch to enter usernames and passwords for authentication, the Switch contacts the TACACS / XTACACS / TACACS+ / RADIUS server to verify, and the server will respond with one of three messages: A) The server verifies the username and password, and the user is granted normal user privileges on the Switch. B) The server will not accept the username and password and the user is denied access to the Switch. C) The server doesn't respond to the verification query. At this point, the Switch receives the timeout from the server and then moves to the next method of verification configured in the method list. The Switch has four built-in server groups, one for each of the TACACS, XTACACS, TACACS+ and RADIUS protocols. These built-in server groups are used to authenticate users trying to access the Switch. The users will set server hosts in a preferable order in the built-in server group and when a user tries to gain access to the Switch, the Switch will ask the first server host for authentication. If no authentication is made, the second server host in the list will be queried, and so on. The built-in server group can only have hosts that are running the specified protocol. For example, the TACACS server group can only have TACACS server hosts. The administrator for the Switch may set up five different authentication techniques per user-defined method list (TACACS / XTACACS / TACACS+ / RADIUS / local / none) for authentication. These techniques will be listed in an order preferable, and defined by the user for normal user authentication on the Switch, and may contain up to eight authentication techniques. When a user attempts to access the Switch, the Switch will select the first technique listed for authentication. If the first technique goes through its server hosts and no authentication is returned, the Switch will then go to the next technique listed in the server group for authentication, until the authentication has been verified or denied, or the list is exhausted. Please note that when the user logins to the device successfully through 頁 : 252 TACACS / XTACACS / TACACS+server or none method, the "user" priviledge level is the only level assigned. If the user wants to get the administration privilege level, the user must use the "enable admin" command to promote his privilege level. However when the user logins to the device successfully through the RADIUS server or through the local method, 3 kinds of privilege levels can be assigned to the user and the user can not use the "enable admin" command to promote to the admin privilege level. If the user has configured the user priviledge attribute of the RADIUS server (example: User A admin level) and the login is successful the device will assign the correct priviledge level (according to the RADIUS server) to the user. However if the user does not configure the user priviledge attribute and logins successfully, the device will assign the "user level" to this user. When assigning the levels 3 is used for the user level, 4 is used for the operator level and 5 is used for the administrator level. 252