HP StorageWorks 8/80 HP StorageWorks Fabric OS 6.1.x administrator guide (5697 - Page 435
FCIP Configuration requirements for FICON extension, Configuration requirements for switches
 |
View all HP StorageWorks 8/80 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 435 highlights
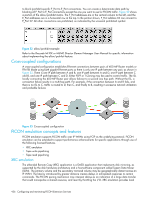
FCIP Configuration requirements for FICON extension FICON extension uses FCIP for transport. FCIP interfaces and tunnels used for FICON extension must be defined prior to configuring FICON emulation. Ports should remain persistently disabled until after FICON emulation is configured. Refer to "Configuring and monitoring FCIP extension services" on page 389 for information about configuring FCIP interfaces and tunnels. Configuration requirements for switches and directors There are three configuration issues to consider when a SAN router is connected to a switch in a FICON configuration. • Ensure enough buffer credits are configured to support extending the FICON channel over distance. • If you are creating a cascaded configuration (connecting two switches or directors with different domain IDs), be aware of IBM requirements for high integrity fabrics. • In configurations with ISLs, ensure that ISL paths are properly configured to meet FICON emulation requirements for a determinate path for FICON commands and responses. Ensure sufficient buffer credits are configured Many switches may have default values that are not sufficient for extending a FICON channel over distance. Having the buffer credits too low may result in device paths not coming online and Fibre Channel aborts. FICON hosts and devices commonly have in excess of 60 credits. A minimum of 60 buffer credits available to all Fibre Channel ports in the path is recommended. High integrity fabric requirements for cascaded configurations Extended FICON connections between or through 400 MP Router models or FR4-18i blade Ethernet interfaces create a cascaded FICON switched configuration. The fabric must be set up to provide a secure, or high integrity fabric to enable this configuration to operate in an IBM environment. See "FICON fabrics" on page 419 for an explanation of these requirements. FICON emulation requirement for a determinate path FICON emulation processing creates FICON commands and responses on extended FICON Channel Path IDs (CHPIDs), and must know exactly what exchanges are occurring between a Channel and a control unit (CU) on a CHPID to function correctly. For FICON Emulation processing to function correctly, the responses to Host I/O (channel I/O) must be carried on the same ISL as the commands. There are three ways to ensure a determinate path for FICON commands and responses: • Define only one IP route and one FCIP tunnel between sites. • Use a traffic isolation zone (TI zone) to • For Brocade M-series directors (6140 and i10K directors), implement the allow/prohibit feature. One Ethernet interface, one IP route and one FCIP tunnel between sites You can ensure a determinate path for FICON commands and responses by configuring only one Ethernet connection between the 400 MP Router SAN routers or FR4-18i blades using only one IP route and one FCIP tunnel. Traffic isolation zoning The Traffic Isolation feature may be used to control the flow of interswitch traffic through the 400 MP Router SAN router or FR4-18i VE_Port or E_Port connections. This feature can be used with Allow/Prohibit settings on M-series directors to create complete flow through paths between end points connected through M-series and FOS products. Traffic isolation uses a special zone, called a traffic isolation (TI zone), to create dedicated paths for specific traffic. You can create a TI zone from either the command line, as described in "Administering Advanced Zoning" on page 193, or from Web Tools. Allow/Prohibit for M-series directors The allow/prohibit feature is available on the Brocade i10k and 6140 M-series directors. This feature enables you to control traffic flow between F_Ports and E_Ports. It is implemented from the Brocade Mi10K or M6140 Director Element Manager GUI through use of an Allow/Prohibit matrix. The matrix allows you Fabric OS 6.1.x administrator guide 435