Cisco IPS-4255-K9 Installation Guide - Page 22
Sensor Interfaces, Understanding Sensor Interfaces
 |
UPC - 746320951096
View all Cisco IPS-4255-K9 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 22 highlights
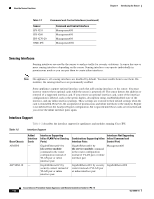
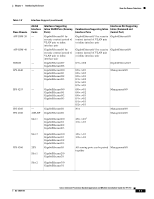
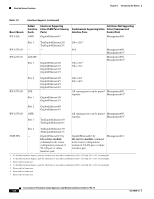
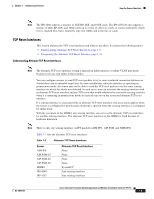
How the Sensor Functions Chapter 1 Introducing the Sensor • Make sure that the event action override is set to drop packets with a risk rating greater than 90. This is the default and ensures that high risk alerts are stopped immediately. • Filter out known false positives caused by specialized software, such as vulnerability scanner and load balancers by one of the following methods: - You can configure the sensor to ignore the alerts from the IP addresses of the scanner and load balancer. - You can configure the sensor to allow these alerts and then use IME to filter out the false positives. • Filter the Informational alerts. These low priority events notifications could indicate that another device is doing reconnaissance on a device protected by the IPS. Research the source IP addresses from these Informational alerts to determine what the source is. • Analyze the remaining actionable alerts: - Research the alert. - Fix the attack source. - Fix the destination host. - Modify the IPS policy to provide more information. For More Information • For a detailed description of risk rating, refer to Calculating the Risk Rating. • For information on Cisco signatures, for IDM and IME refer to Defining Signatures, and for the CLI refer to Defining Signatures. • For detailed information on event action overrides, for IDM and IME refer to Configuring Event Action Overrides, and for the CLI, refer to Configuring Event Action Overrides. • For information on using Cisco IME, refer to Installing and Using Cisco Intrusion Prevention System Manager Express 7.0. Sensor Interfaces This section describes the sensor interfaces, and contains the following topics: • Understanding Sensor Interfaces, page 1-4 • Command and Control Interface, page 1-5 • Sensing Interfaces, page 1-6 • Interface Support, page 1-6 • TCP Reset Interfaces, page 1-9 • Interface Restrictions, page 1-10 Understanding Sensor Interfaces The sensor interfaces are named according to the maximum speed and physical location of the interface. The physical location consists of a port number and a slot number. All interfaces that are built-in on the sensor motherboard are in slot 0, and the PCI expansion slots are numbered beginning with slot 1 for the bottom slot with the slot numbers increasing from bottom to top (except for the IPS 4270-20, where the Cisco Intrusion Prevention System Appliance and Module Installation Guide for IPS 7.0 1-4 OL-18504-01