Netgear GS418TPP User Manual - Page 294
Local, RADIUS, TACACS, Apply, Method 2 and Method 3.
 |
View all Netgear GS418TPP manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 294 highlights
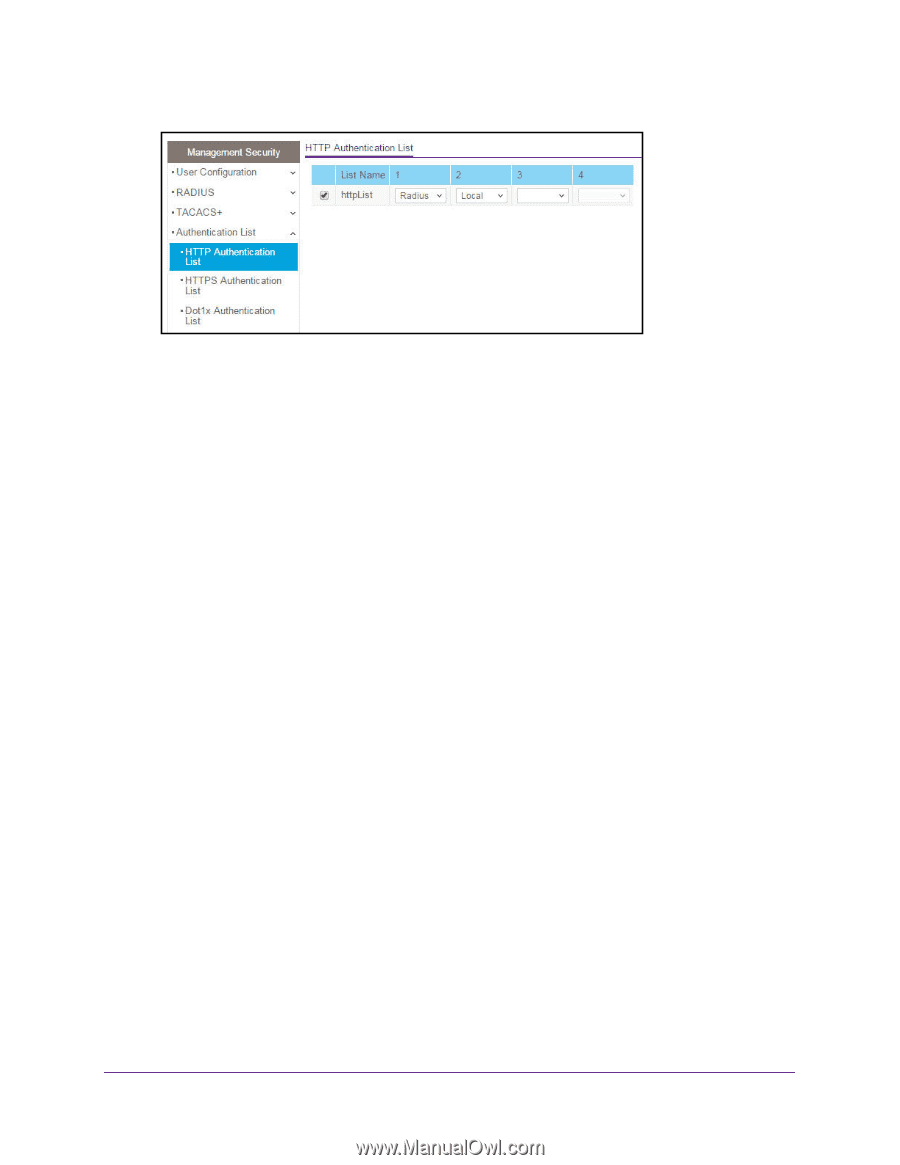
ProSAFE 8-Port or 16-Port Gigabit Smart Managed Switch Model GS418TPP, GS510TLP, and GS510TPP 6. Select the check box next to the httpList name. 7. From the menu in the 1 column, select the authentication method that must be used first in the selected authentication login list. If you select a method that does not time out as the first method, such as Local, no other method is tried, even if you specified more than one method. User authentication occurs in the order the methods are selected. Possible methods are as follows: • Local. The user's locally stored ID and password are used for authentication. Since the Local method does not time out, if you select this option as the first method, no other method is tried, even if you specified more than one method. • RADIUS. The user's ID and password are authenticated using the RADIUS server. If you select RADIUS or TACACS+ as the first method and an error occurs during the authentication, the switch uses Method 2 to authenticate the user. • TACACS+. The user's ID and password are authenticated using the TACACS+ server. If you select RADIUS or TACACS+ as the first method and an error occurs during the authentication, the switch attempts user authentication Method 2. • None. The authentication method is unspecified. This option is available only for Method 2 and Method 3. 8. From the menu in the 2 column, select the authentication method, if any, that must be used second in the selected authentication login list. This is the method that is used if the first method times out. If you select a method that does not time out as the second method, the third method is not tried. 9. From the menu in the 3 column, select the authentication method, if any, that must be used third in the selected authentication login list. 10. From the menu in the 4 column, select the method, if any, that must be used fourth in the selected authentication login list. This is the method that is used if all previous methods time out. 11. Click the Apply button. The updated configuration is sent to the switch. Configuration changes take effect immediately. Manage Device Security 294